With the ever-increasing number of cyber-attacks, data breaches, and security threats, companies are now embracing new approaches to safeguard their sensitive information. Zero Trust Architecture is one such approach that has proven to be very effective in protecting data against unauthorized access, malware, phishing attacks, and other types of cyber threats. Zero Trust Architecture provides a comprehensive defense system for organizations using software composition analysis, identity, access management tools, secure authentication protocols, and other security measures.
What is Zero Trust Architecture, and Why is it Important for Cybersecurity?
Zero Trust Architecture is a cybersecurity model designed to provide a secure network environment by limiting user privileges and access to resources based on specific contextual and environmental factors such as the user’s identity, location, device, etc. Unlike traditional security models, where users are granted access based on their physical location or network, Zero Trust Architecture applies a “never trust, always verify” approach to ensure that only authorized users gain access to sensitive data. This approach is critical for cybersecurity because it reduces the risk of data breaches, prevents the spread of malware and other cyber threats, and protects against insider threats.
Exploring the Benefits of Zero Trust Architecture
The primary benefit of Zero Trust Architecture is that it provides an added layer of security to protect against cyber threats. This is because users are required to go through several layers of authentication, such as multi-factor authentication, before gaining access to the network. By applying a “least privilege” access model, companies can significantly minimize data breaches by limiting user privileges and resource access based on specific contextual and environmental factors. Additionally, organizations that adopt Zero Trust Architecture can reduce their exposure to malware and phishing attacks.
Another benefit of Zero Trust Architecture is that it can be easily integrated with existing security systems. For instance, companies can incorporate a Zero Trust model with their SIEM (Security Information and Event Management) systems to monitor and detect suspicious activities within the network.
Major Components of a Zero Trust Model
- Identity and Access Management (IAM): This component ensures that only authorized users can access specific resources based on their roles and privileges. It involves user authentication, authorization, and ongoing monitoring of user access.
- Microsegmentation: This involves dividing the network into smaller segments or zones, each with its own security policies and access controls. Doing so limits lateral movement within the network and minimizes the potential impact of a security breach.
- Network Security: In a Zero Trust Model, network security encompasses the use of firewalls, intrusion detection and prevention systems (IDPS), secure web gateways, and other tools to monitor and control traffic entering and leaving the network.
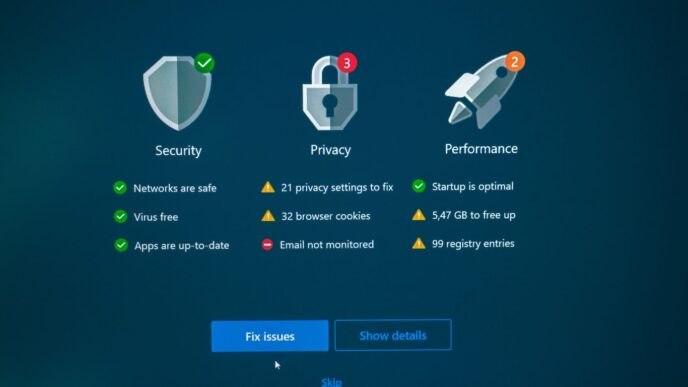
- Endpoint Security: This component focuses on securing all devices that connect to the network, including desktops, laptops, smartphones, and IoT devices. Endpoint security measures may include antivirus software, encryption, and device management solutions to ensure compliance with security policies.
- Data Security: Data security protects sensitive information from unauthorized access, modification, or destruction. Measures include data classification, encryption, tokenization, and data loss prevention (DLP) solutions.
- Application Security: This component includes securing applications against vulnerabilities and attacks, such as SQL injection, cross-site scripting, and buffer overflows. Application security measures may involve code reviews, vulnerability scanning, and the use of web application firewalls (WAF).
Understanding the Different Types of Authentications Used in a Zero Trust Model
Zero Trust Architecture relies on multiple layers of authentication to ensure that only authorized users have access to sensitive data. The different types of authentications used in a Zero Trust Model include:
- Multi-Factor Authentication: This involves the use of multiple authentication factors, such as a password and a one-time code sent via text message or email.
- Risk-Based Authentication: This involves the use of contextual factors, such as the location of the user, the time of day, and the device used, to assess the risk level of an authentication request.
- Adaptive Authentication: This involves using a combination of authentication factors and contextual data to determine the level of risk associated with an authentication request.
Implementing a Zero Trust Model to Minimize Risks
Implementing a Zero Trust Architecture model is a complex process that involves several steps. These steps include:
- Network Segmentation: Network segmentation involves dividing the network into smaller pieces to reduce the attack surface area.
- Identity and Access Management: Involves creating policies that dictate user access privileges and authentication requirements.
- Risk Assessment: This involves assessing the risk level associated with different resources, users, and devices.
- Continuous Monitoring: It involves using security tools and technologies to monitor and detect suspicious activities within the network.
Looking Ahead at the Future of Security with Zero Trust Architecture
As cyber threats evolve, so must cybersecurity approaches and strategies. Zero Trust Architecture is at the forefront of this evolution, providing an effective and comprehensive security model that can help organizations protect their networks from malicious actors.
It’s important to note that implementing a Zero Trust Architecture is only one component of a comprehensive security system. Organizations must also ensure they have adequate policies in place and invest in robust monitoring systems to detect suspicious behavior quickly. In addition, companies should work with cybersecurity professionals to develop tailored security plans designed for their unique needs and risks.
Common Pitfalls of Building a Zero Trust System
While Zero Trust Architecture is an incredibly powerful security model, there are still several pitfalls that companies must be aware of to ensure the most effective implementation. These common pitfalls include:
- Overly Complex Implementation Process: A complex implementation process can lead to delays in deployment and a lack of user understanding and adoption.
- Lack of Security Awareness Training: Without proper training, users may not undergo and use the system properly, inadvertently creating security vulnerabilities.
- Inadequate User Access Policies: If policies are too lenient or fail to take into account contextual factors, malicious actors may be able to access sensitive data despite authentication requirements.