Looking back at 2018, it was a pretty busy year for the internet of things, or IoT as everyone calls it. Lots of smart people were writing about how these connected devices work, how to keep them safe, and what kinds of tech were making it all possible. We’ve pulled together some of the most interesting internet of things articles from that year to give you a good overview of what was happening. It’s a snapshot of where things stood back then, covering everything from the basic setup to the big security worries.
Key Takeaways
- In 2018, a lot of attention was on how to build and structure internet of things systems, looking at different ways to set them up and make them work efficiently.
- Security was a major concern, with many articles discussing the various threats facing IoT devices and exploring ways to protect them.
- Understanding the communication methods, or protocols, used by IoT devices was key, with reviews covering how different devices talk to each other and the cloud.
- The landscape of security threats was constantly changing, and researchers were busy identifying new dangers and how they worked.
- Machine learning started playing a bigger role in IoT security, with studies looking at how AI could help detect and prevent cyber attacks on connected devices.
Exploring Internet Of Things Architectures In 2018
In 2018, the way we thought about how the Internet of Things (IoT) was put together really started to solidify. It wasn’t just about connecting devices anymore; it was about building smart, layered systems. People were looking at how to make these systems work efficiently and securely.
Reference Architectures For The Internet Of Things
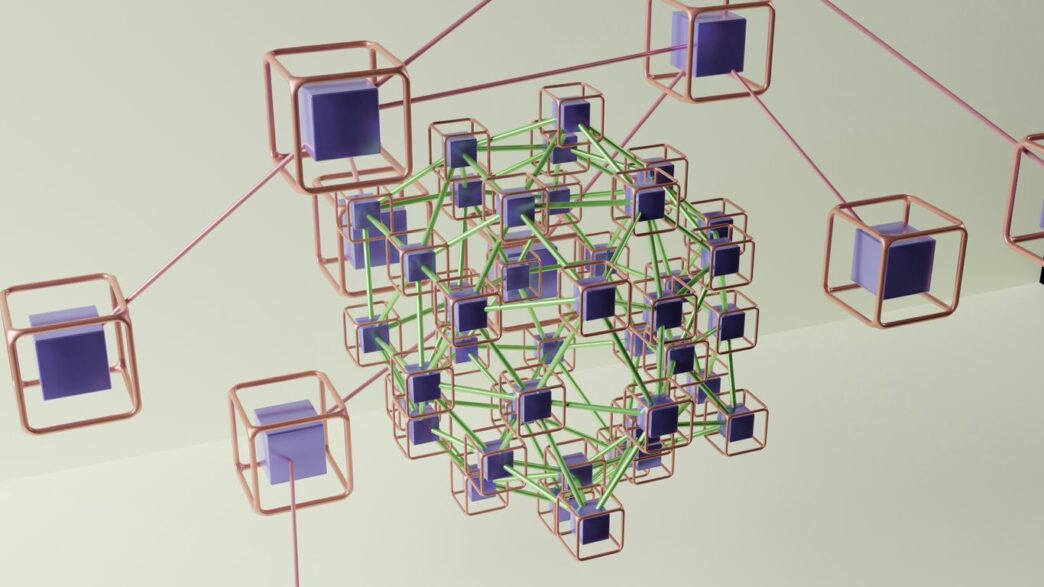
When you’re building something complex like an IoT system, having a blueprint is super helpful. Reference architectures act like those blueprints. They aren’t a one-size-fits-all solution, but they give you a solid starting point and a common language to talk about different parts of the system. Think of them as guides that show you the main components and how they might interact. In 2018, there was a lot of discussion around established models like IoT-A and IIRA, which aimed to bring different IoT ideas together into a more unified structure. These architectures often break down the system into layers, like the perception layer (where sensors and devices live), the network layer, and the application layer.
A Software Defined Networking Architecture For The Internet Of Things
Software-Defined Networking (SDN) started making waves in the IoT space. The idea here is to separate the network’s control functions from the actual data forwarding. This makes the network more flexible and easier to manage. For IoT, this meant being able to control and configure network traffic more dynamically, which is a big deal when you have so many different devices with varying needs. An SDN approach could help manage things like quality of service and make it simpler to deploy and scale IoT networks. It’s like having a central control panel for your entire network, rather than fiddling with individual devices.
What Is IoT Architecture?
At its core, IoT architecture is all about how the different pieces of an IoT system fit together. It’s the structure that allows devices to collect data, send it somewhere, have it processed, and then act on it. Most architectures involve several layers. You’ve got the devices themselves, often called the perception layer, which gather information from the environment. Then there’s the network layer, which handles communication. After that, you might have a middleware layer for processing and a final application layer where users interact with the data or control the system. Understanding these layers and how they communicate is key to building a functional and reliable IoT system. It’s not just about the hardware; it’s about the whole ecosystem working in harmony.
Key Security Challenges And Solutions For Internet Of Things In 2018
The year 2018 saw the Internet of Things (IoT) continue its rapid expansion, but this growth brought a bigger target for cyber threats. With so many devices connecting, the potential attack surface grew exponentially. It’s tough to keep IoT systems secure, partly because the devices themselves often have limited resources and are left in places where they can’t be easily monitored. Trying to use standard security methods like encryption or access control just doesn’t cut it when you have millions of devices, each with its own weak spots.
Many users and even developers weren’t fully aware of the risks, which left doors open for attacks. We saw this with things like the Mirai botnet, which exploited these vulnerabilities. The consequences aren’t just digital; compromised sensors in things like self-driving cars could lead to real-world accidents and damage. It’s clear that IoT security can’t be an afterthought; it needs to be a top priority.
A Survey On Attacks In Internet Of Things Based Networks
Looking back at 2018, researchers were busy cataloging the many ways IoT networks could be attacked. The main goal was always to protect the integrity, confidentiality, and availability of data for regular users. Surveys from this period highlighted a wide range of potential threats, their characteristics, and the difficulties in dealing with them.
- Denial of Service (DoS) Attacks: Overwhelming devices or networks to make them unavailable.
- Man-in-the-Middle (MitM) Attacks: Intercepting communication between devices.
- Malware and Botnets: Infecting devices to use them for malicious purposes, like the infamous Mirai botnet.
- Physical Tampering: Directly accessing and altering devices.
Towards Security On Internet Of Things: Applications And Challenges In Technology
Securing IoT applications presented a unique set of hurdles. The sheer variety of devices, from tiny sensors to complex industrial controllers, meant that a one-size-fits-all security approach was impossible. Researchers pointed out that the limited processing power and memory on many IoT devices made it difficult to implement robust security measures. Furthermore, the lack of standardized security protocols across different manufacturers added another layer of complexity. The interconnected nature of IoT means a vulnerability in one device can potentially compromise an entire network.
A Roadmap For Security Challenges In The Internet Of Things
In response to these growing concerns, efforts were made in 2018 to create clearer paths forward for IoT security. This involved looking at security from a systemic perspective, considering everything from individual devices to the entire ecosystem. Key areas identified included:
- Device-Level Security: Implementing secure boot processes and ensuring devices are updated regularly.
- Network Security: Protecting the communication channels between devices and the cloud.
- Data Security and Privacy: Safeguarding the information collected by IoT devices.
- Authentication and Access Control: Making sure only authorized users and devices can access resources.
These roadmaps aimed to provide a structured way to address the multifaceted security challenges inherent in the expanding world of IoT.
Understanding Internet Of Things Protocols And Their Applications
When we talk about the Internet of Things (IoT), it’s easy to get caught up in the shiny new devices and the big picture of smart homes or cities. But underneath all that, there’s a whole world of communication happening, and that’s where protocols come in. Think of them as the languages that IoT devices use to talk to each other and to us. Without them, your smart thermostat wouldn’t know to tell your smart AC to turn on, or your fitness tracker wouldn’t send your workout data to your phone.
Analysis Of Different IoT Protocols For Heterogeneous Devices And Cloud Platform
One of the big headaches in IoT is that not all devices are created equal. You’ve got tiny sensors that barely have enough power to send a text message, and then you’ve got more complex devices that need to send a lot more data. This is why there are so many different protocols out there. Some are built for low power and low data rates, like MQTT (Message Queuing Telemetry Transport), which is super popular for sending small bits of data from many devices. Others are more robust and can handle bigger data streams, often used when devices need to communicate directly with cloud platforms. The challenge is making sure these different devices and platforms can actually understand each other. It’s like trying to have a conversation when everyone speaks a different dialect.
Internet Of Things (IoT) Communication Protocols: Review
Looking back at 2018, a lot of research was focused on sorting through the mess of IoT protocols. We saw reviews that broke down the pros and cons of various options. For instance, CoAP (Constrained Application Protocol) is designed for constrained devices, meaning those with limited processing power and memory. It’s often compared to HTTP but is much lighter. Then there’s AMQP (Advanced Message Queuing Protocol), which is more suited for enterprise-level messaging, offering features like message queuing and reliable delivery. The choice of protocol really depends on the specific needs of the IoT application, from power consumption to data volume and security requirements. It’s not a one-size-fits-all situation, and understanding these differences is key to building a functional IoT system. You can find a good overview of these in various IoT communication protocols.
Internet Of Things: Architectures, Protocols, And Applications
Ultimately, protocols are just one piece of the puzzle. They fit into the larger picture of IoT architectures, which define how devices, networks, and applications are put together. A typical architecture might involve devices collecting data, sending it through a network (using specific protocols), processing it in the cloud, and then presenting it to users through an app or dashboard. The applications are where we see the real impact – from smart agriculture that helps farmers optimize crop yields to intelligent transportation systems that try to ease traffic jams. But as these systems grow, so do the complexities of managing the communication between all the different parts. It’s a constant balancing act between making things work smoothly and keeping them secure.
The Evolving Landscape Of Internet Of Things Security Threats

The world of the Internet of Things (IoT) exploded in 2018, and with that growth came a whole new set of security headaches. It’s like building a massive city without thinking too much about locks on the doors. As more devices got connected, the potential for bad actors to cause trouble grew right along with it. We saw a real shift from just worrying about individual device security to looking at the whole system, the entire architecture, and how everything talks to each other. This was a big step because, honestly, many manufacturers were just focused on getting their cool new gadgets out the door, not necessarily making them super secure.
This often meant that devices were easy targets. Remember the Mirai botnet? That was a wake-up call for many, showing how compromised devices could be used for massive attacks. It wasn’t just about stealing data anymore; the potential for real-world damage, like messing with self-driving cars or critical infrastructure, became a serious concern. The sheer number of connected devices, often with limited processing power and left in unattended places, made traditional security methods tough to implement. The attack surface just kept getting bigger and bigger.
Here’s a look at some of the key threats that were making waves:
- Botnets: Networks of compromised devices, like those seen in the Mirai attack, used to launch large-scale distributed denial-of-service (DDoS) attacks.
- Malware: Worms, viruses, and spam specifically designed to exploit vulnerabilities in IoT software and hardware.
- Zero-Day Exploits: Attacks that take advantage of previously unknown vulnerabilities before a patch is available.
- Data Breaches: Unauthorized access to sensitive information collected by IoT devices.
Researchers were busy trying to map out all these new dangers. They looked at how attacks happened across different layers of IoT systems, from the device itself all the way up to the cloud. It was clear that a more structured approach to security was needed, moving beyond just basic encryption and passwords. Understanding the anatomy of these threats was the first step toward building better defenses for the connected future. This research into IoT security was becoming more important than ever.
Advancements In Machine Learning For Internet Of Things Security

So, 2018 was a pretty interesting year for figuring out how to make the Internet of Things (IoT) more secure, and a big part of that involved using machine learning (ML). It’s like teaching computers to spot weird stuff happening on networks, kind of like how we learn to recognize when something’s not quite right in our own lives. Researchers were really digging into how ML could help identify attacks and keep our connected devices safer.
Machine Learning Approaches To IoT Security: A Systematic Literature Review
Lots of studies came out looking at how different ML methods could be used for IoT security. The goal was to find ways to automatically detect threats without needing a person to constantly watch over everything. Some approaches focused on spotting unusual activity, like a smart thermostat suddenly sending out way more data than it normally does. Others tried to classify different types of network traffic to flag anything suspicious. The big challenge was often getting enough good data to train these ML models effectively. It’s tough because IoT networks can be so diverse, with all sorts of devices speaking different ‘languages’.
Evaluating Shallow And Deep Neural Networks For Network Intrusion Detection Systems
When we talk about ML, neural networks are a big deal. In 2018, people were looking at both simpler (shallow) and more complex (deep) neural networks for spotting intrusions. Shallow networks are like the basic models, while deep networks have more layers, allowing them to learn more intricate patterns. Think of it like this:
- Shallow Networks: Good for recognizing straightforward patterns, like a known type of attack.
- Deep Networks: Can pick up on more subtle, complex threats that might be missed by simpler methods.
Researchers were testing these out to see which ones worked best for identifying things like denial-of-service attacks or unauthorized access attempts on IoT devices. It’s a bit like trying out different tools to see which one is best for a specific job.
Deep Learning Models For Cyber Security In IoT Networks
Deep learning, a subset of ML, really started to get attention for IoT security. These models, with their many layers, are powerful for analyzing large amounts of data and finding hidden connections. For instance, some researchers explored using deep learning to analyze network traffic patterns and identify anomalies that could signal a security breach. Others looked at how these models could help in classifying malware specifically designed for IoT devices. It’s a promising area because the sheer volume and variety of data generated by IoT devices make them a prime candidate for sophisticated analysis techniques. The idea is that by learning from vast datasets, these models can become really good at predicting and preventing cyber threats before they cause real damage.
Internet Of Things Vulnerabilities And Mitigation Strategies
Internet Of Vulnerable Things? Threat Architecture, Attack Surfaces, And Vulnerabilities
So, 2018 was a big year for the Internet of Things, right? More devices, more connections, more smart stuff everywhere. But with all that growth comes a bigger target. Think about it: your smart fridge, your thermostat, even your car – they’re all connected. And where there’s a connection, there’s a potential weak spot.
One of the main issues is how exposed these devices often are. They’re sitting out there, sometimes in plain sight, making them easy targets for physical tampering or even firmware cloning. Imagine someone getting their hands on your car’s controller bus – not a good thought. Then there’s the whole booting process. If a device doesn’t properly check what it’s loading when it starts up, attackers can sneak in malicious code right from the get-go. We saw this with some early smart devices, and it’s a real headache.
Network vulnerabilities are another huge area. This is where things like weak passwords, or no passwords at all, really come into play. Many IoT devices still use default credentials, which are basically an open invitation. Plus, the encryption they use might not be up to par for lightweight devices, leaving data exposed. This can lead to all sorts of problems, from denial-of-service attacks to data theft. And in critical areas like healthcare, compromised devices like insulin pumps could have serious consequences.
IoT Vulnerability Assessment For Sustainable Computing: Threats, Current Solutions, And Open Challenges
It’s not just about the hardware, though. Software plays a massive role. Using outdated software or libraries, or just plain weak programming practices, creates openings. Attackers can exploit these known flaws to gain access. The infamous Mirai botnet, for example, took advantage of open ports and weak passwords to build a massive army of compromised devices. They basically scanned for devices with open telnet ports and then tried common or default login details. It’s a bit like leaving your front door unlocked and hoping for the best.
So, what are we doing about it? Well, there are efforts to create better security frameworks and taxonomies to understand these attacks. Researchers are looking into different ways to secure these devices, from better authentication methods to more robust encryption. But it’s a constant cat-and-mouse game. The challenges are pretty significant, especially with the sheer number of devices and their limited resources. We’re still figuring out the best ways to assess these vulnerabilities and build more secure IoT systems for the long haul.
Top 10 IoT Vulnerabilities
To give you a clearer picture, here are some of the most common vulnerabilities that popped up in discussions back in 2018:
- Weak, guessable, or hardcoded passwords: This is probably the most common and easiest to exploit. Default credentials are a hacker’s best friend.
- Insecure network services: Devices often have unnecessary ports open or use unencrypted communication protocols.
- Insecure ecosystem interfaces: This covers things like web, cloud, or mobile interfaces that aren’t properly secured, allowing unauthorized access.
- Lack of device management: No easy way to update firmware, manage devices, or revoke access when needed.
- Insecure default settings: Devices shipping with security features turned off or set to insecure defaults.
- Lack of secure update mechanisms: If updates can’t be delivered securely, attackers can push malicious firmware.
- Use of Insecure or Outdated Components: Relying on old software libraries with known vulnerabilities.
- Insufficient privacy protection: Not handling user data securely or transparently.
- Insecure data transfer and storage: Sending sensitive data over unencrypted channels or storing it insecurely.
- Lack of product security guidance: Manufacturers not providing clear instructions on how to secure their devices.
Looking Back and Moving Forward
So, 2018 was quite a year for the Internet of Things, wasn’t it? We saw a lot of talk about how these connected devices are changing everything, from our homes to big industries. It felt like every other article was discussing new ways to use sensors, better ways to connect things, and, of course, the big one: security. It’s clear that while the potential is huge, there are still plenty of hurdles to jump over. As we wrap up this look back, it’s exciting to think about what’s next. The conversations from 2018 set the stage for where we are now, and it’s a good reminder that this whole IoT thing is still very much a work in progress.
Frequently Asked Questions
What exactly is the Internet of Things (IoT)?
Think of the Internet of Things, or IoT, as a giant network where everyday objects, like your fridge or your watch, can connect to the internet. They can then share information and even talk to each other, making our lives easier and more connected.
Why was 2018 a big year for IoT?
In 2018, lots of important research and development happened in IoT. People were figuring out the best ways to build these connected systems (architectures), how to keep them safe from hackers (security), and what languages or rules (protocols) these devices should use to communicate.
What are some common security problems with IoT devices?
Because so many devices are connected, they can become targets for bad actors. Some common issues include weak passwords, devices not being updated with security patches, and sometimes even devices being used to launch attacks on others, like in a botnet.
How is machine learning used to make IoT more secure?
Machine learning, which is like teaching computers to learn from data, is used to spot unusual activity on the network. It can help detect when a device is acting strangely, which might mean it’s been hacked, and alert us to the problem.
What are IoT protocols, and why are they important?
Protocols are like the rules of the road for IoT devices. They tell devices how to send and receive information. Different protocols are good for different things, like sending small amounts of data quickly or connecting many devices at once.
What are some ways to fix or avoid IoT security problems?
Fixing IoT security involves several steps. This can include using strong, unique passwords, making sure devices are updated regularly, designing systems with security in mind from the start, and being aware of common weaknesses that hackers look for.