As we navigate the constantly changing terrain of the digital world, the importance of cybersecurity for businesses has never been more pronounced. With cybercriminals employing ever-more advanced techniques, it’s clear that traditional cybersecurity strategies may no longer suffice. Continuous Adversary Emulation (CAE), an innovative approach that could redefine how enterprises protect themselves in 2024 and beyond. But how exactly does CAE transform the way businesses safeguard against cyber threats?
BuddoBot, a veteran and minority-owned business specializing in offensive cybersecurity, is leading this change in how threats are detected. By continuously emulating real-world attacks, they surpass the limitations of traditional cybersecurity methods like automated scanning and compliance checks. Their team of professional hackers and security experts crafts custom solutions, using realistic attack vectors to identify and mitigate potential breaches before they happen.
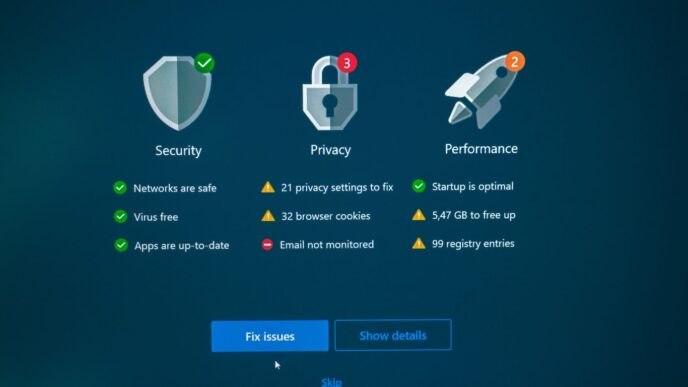
Luke Secrist, CEO of BuddoBot, emphasizes the importance of this continuous approach: “You scan your network for vulnerabilities, so it should be secure, right? Think again. Many companies conduct cybersecurity audits or penetration tests (PenTests) once a year, maybe every six months. Annual audits may report everything is alright, but is it really? One cybersecurity audit won’t fix all your problems. It’s just a snapshot; tomorrow’s issues may not exist today, and today’s fix may not apply tomorrow.”
In the field of IT services, it’s a well-known fact that system vulnerabilities can surface unexpectedly. The rapid pace of change in technology means that new threats can emerge at any moment, often catching organizations off guard. This reality underscores the need for a more dynamic approach to cybersecurity.
Secrist further explains the limitations of periodic testing: “Criminal hackers don’t attack based on schedules. In fact, these criminals seek out organizations they believe are just ‘checking a box’ for security compliance.” This strategy of targeting complacent organizations highlights the necessity for enterprises to adopt proactive measures.
Continuous Adversary Emulation (CAE) offers a solution. Unlike traditional methods, CAE involves a relentless and ongoing process of simulating attacks, mirroring the persistent nature of cybercriminals. This approach allows for the identification of vulnerabilities in real-time, providing organizations with the opportunity to strengthen their defenses continuously.
The essence of CAE lies in its ability to mimic the tactics and strategies of real-world attackers. By understanding how cybercriminals operate, organizations can anticipate potential threats and implement more effective countermeasures. This shift from a reactive to a proactive stance in cybersecurity is vital for businesses looking to protect their digital assets in 2024.
Moreover, CAE’s continuous nature ensures that security measures are always up-to-date with the latest threats. This is crucial in a digital world where cyber threats evolve rapidly, often outpacing traditional security updates.
The integration of CAE into an organization’s cybersecurity strategy also fosters a culture of ongoing vigilance and adaptation. It encourages IT teams and decision-makers to stay informed about emerging cyber threats and adjust their defenses accordingly.
In conclusion, as enterprises traverse the complex cybersecurity landscape of 2024, the implementation of Continuous Adversary Emulation (CAE) emerges as a critical strategy to outpace cyber threats. In a world where cybercriminals are ceaselessly refining their tactics, a dynamic and proactive approach to digital defense has become indispensable. For instance, consider a financial institution that employs CAE: by continuously simulating phishing attacks and testing their network’s response, they can identify and address vulnerabilities before actual threats materialize. Similarly, a healthcare provider using CAE can regularly test their systems against ransomware attacks, ensuring patient data remains secure and accessible even under potential cyber assaults. As Luke Secrist of BuddoBot suggests, adopting the mindset of an adversary and regularly evolving cybersecurity practices are vital for ensuring robust digital protection in today’s ever-changing cyber environment.