A distributed denial of service (DDoS) attack describes a cybercrime that weaponizes the scale of modern internet traffic. Long feared for its ability to cut organizations and individuals off from genuine online users, the DDoS is a persistent and evolving threat in an increasingly digital world.
What is a DDoS?
Nowadays, local storage is rare – cloud and third-party services mean that the internet sees a staggering 7.7 Exabytes of traffic per day; for context, 1 exabyte represents a billion gigabytes. Let’s narrow the scope a little, and analyze the process of loading a webpage. When you request a site, that request travels from your browser to the hosting server. The server dedicates a small amount of processing power in order to find and deliver said page. The hosting body – whether that’s an on-premises server stack or an outsourced cloud provider – has an implicit limit to the number of requests that can be made at one time. For on-premises physical servers, this is a hard line: the resource pool, once used up, simply cannot sustain high levels of traffic. Cloud providers, with their more flexible approaches, can keep a page up – at greater cost to the site owner.
This infrastructure works incredibly well for legitimate users: businesses and organizations can benefit from a site’s steady increase in popularity, reaping the rewards of high click-through and interaction rates.
A DDoS turns this process on its head, striking a business or organization at its most public point. The hosting server is flooded with illegitimate network traffic, and the server provider is left to battle the flood. On-premises solutions are almost always completely crippled by these attacks, while cloud customers are often faced with a monstrous bill as more processing power is demanded.
DDoS attacks are an extended form of Denial of Service attack. This describes a malicious actor using a single internet connection to barrage a target with illegitimate site requests. Though a powerful disruption tactic at its core, the DoS is easily combated via IP address blocking. DDoS ramps up both the destructive potential and evasion difficulty by copying this format across thousands – or even millions – of Wi-Fi-connected devices.
These distributed networks of attacker-controlled devices are called botnets. Botnets are formed through the compromise of average users’ devices. This is possible through various forms of malware, commonly planted on Wi-Fi-connected devices via phishing attacks or zero-day vulnerabilities. The legitimate user of the device often has no idea that in the background, their PC is taking part in a global cyberattack. It’s not just laptops and PCs that are hijacked.
One of the most powerful DDoS botnets is primarily comprised of Wi-Fi-connected Internet of Things (IoT) devices, such as smart fridges, baby monitors, and smart doorbells. This is thanks to the incredibly lax security often surrounding these devices. The Mirai botnet has single-handedly almost brought down the internet multiple times, the worst of which occurred in 2016, as it left much of the U.S. east coast without internet.
2022: The Rise of a New Form of DDoS
DDoS attacks have scaled to immeasurable extremes, but are largely limited by the resources that orchestrating such large attacks demands. This means that targeted attacks may have previously occurred between infighting cybercriminal groups, or as secondary items to ransomware attacks. Now, however, the focus on DDoS’ visibility has seen one group in particular take note: global governments.
So far in 2022, the global relationships between country leaders have somewhat deteriorated. This has had major repercussions on the intensity, and geography of DDoS attacks, which are now being actively used for political purposes. On the 23rd of February, Ukraine experienced some of the worst geopolitical cyberattacks it had ever witnessed, experiencing major disruptions to services within the banking and governmental servers. The day after, on the 24th of February, Russian troops crossed the border, greatly escalating the Russia-Ukraine War.
As the conflict progressed, more DDoS attacks struck. On April 8th, the websites of Finland’s defense and foreign affairs ministries suddenly went down. Banking infrastructure was also hit, with some customers unable to access their savings account for a day. Note that the point of these DDoS attacks are not to genuinely disrupt the daily working lives of people: by striking public-facing communication infrastructure, Russia-backed hackers are sending a clear, public message. On the 4th April, Helsinki had publicly admitted to a shift in foreign policy, drawing them closer to NATO.
Whereas Russia has used DDoS attacks in an attempt to instill fear into the governments opposing its geopolitical choices, China has shown considerably more restraint in its DDoS propaganda machine. On March 11th, state news agency Xinhua claimed that IP addresses based in the US, Germany and the UK had seized Chinese computers and targeted Belarus, Russia and Ukraine. After all, China does not engage in DDoS attacks.
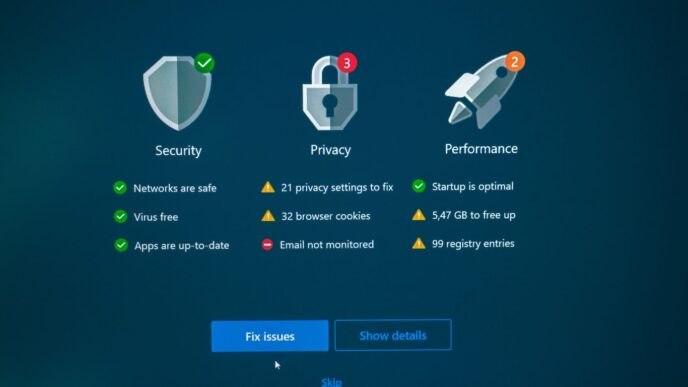
Protecting Against DDoS Attacks
DDoS attacks can only be stopped by mitigation programs. One of the most cost-effective and efficient forms of mitigation is establishing a Border Gateway Protocol (BGP). Once traffic hits an assault threshold, an announcement is triggered, ensuring that incoming traffic is routed through a set of scrubbing centers. Powerful servers within the scrubbing centers then identify and filter out malicious packets, forwarding the clean traffic onto your own server.
With mitigation processes firmly in place, you can guarantee continued service to genuine users and customers, whilst also preventing any attempt to make you part of a propaganda machine.