In today’s digital age, cybersecurity has become more important than ever before. From protecting our personal information to safeguarding sensitive business data, we must understand the basics of cybersecurity and how to stay safe online. In this blog post, we’ll demystify the world of cybersecurity by exploring what it is, why it matters, and, most importantly, practical tips on how you can protect yourself against cyber threats.
What is Cybersecurity?
The term “cybersecurity” is used a lot these days, but what does it mean? Simply put, cybersecurity is the practice of protecting your computer networks and user data from unauthorized access or theft. This can include anything from installing firewalls and anti-virus software to developing secure coding practices and conducting regular security audits.
Why is cybersecurity important? In our increasingly connected world, cyberattacks are becoming more common. These attacks can have serious consequences, ranging from financial loss to reputational damage to data breaches that expose sensitive information. By taking steps to improve your cybersecurity, you can help protect your business or organization from these risks.
What are some simple things you can do to stay safe online? Here are a few tips:
- Keep your software up to date: Regular updates can help patch vulnerabilities that could be exploited by hackers.
- Use strong passwords: Long, randomized passwords are more difficult for attackers to guess. Consider using a password manager to help keep track of them.
- Beware of phishing emails: Don’t click on links or open attachments from unknown senders. If an email looks suspicious, delete it.
- Back up your data: This way, if you do experience data loss due to a cyberattack, you’ll be able to recover your files quickly and get back up and running.
Types of CyberAttacks
There are many types of cyberattacks, but some of the most common include:
1. Malware: Malicious software, or malware, is any program or file that is designed to harm your computer or steal your personal information. Viruses, worms, and Trojans are all types of malware.
2. Phishing: Phishing is a type of online fraud that attempts to trick you into sharing personal or financial information. Scammers may send fake emails or set up fake websites that look like legitimate businesses to get your information.
3. Denial-of-service (DoS) attacks: A DoS attack is an attempt to make a website or network unavailable by flooding it with traffic or requests for data. DoS attacks can be very disruptive and cause significant financial losses.
4. SQL injection: SQL injection is a type of attack that allows attackers to execute malicious code on a database server. This type of attack can compromise the security of an entire website or application.
5. Cross-site scripting (XSS): XSS attacks exploit vulnerabilities in web applications to inject malicious code into web pages that are viewed by other users. This type of attack can be used to steal sensitive information or hijack user accounts.
The Impact of Cybercrime
Cybercrime is a growing problem in today’s world. With the advent of the internet, criminals have found a new way to commit crimes. Cybercrime can include anything from identity theft and fraud to hacking and denial-of-service attacks.
The impact of cybercrime can be far-reaching. Victims of cybercrime can suffer financial losses, damage to their reputations, and even emotional distress. In some cases, cybercrime can even lead to physical harm.
There are steps that you can take to protect yourself from cybercrime. Be sure to use strong passwords and never share them with anyone. Additionally, keep your personal information private and be cautious about what you share online. By taking these precautions, you can help reduce your risk of becoming a victim of cybercrime.
Best Practices for Protecting Yourself Online
When it comes to cybersecurity, there are a few best practices that everyone should follow to stay safe online. First and foremost, you should always use strong passwords for all of your online accounts. A strong password is at least eight characters long and includes a mix of upper- and lower-case letters, numbers, and symbols. You should never use the same password for more than one account, and you should avoid using easily guessed words like “password” or your name.
In addition to using strong passwords, you should also enable two-factor authentication (2FA) whenever possible. 2FA adds an extra layer of security to your accounts by requiring you to enter a code from your phone or another device in addition to your password. This makes it much harder for hackers to gain access to your accounts, even if they have your password.
You should also be careful about the information you share online. Be cautious about what you post on social media and think twice before sharing personal information like your address or date of birth publicly. When creating new online accounts, only provide the minimum amount of information required. And be sure to keep an eye out for phishing scams, which are attempts by hackers to trick you into giving them sensitive information by masquerading as a trusted website or person.
By following these best practices, you can help keep yourself safe from many common cyber threats.
Understanding Different Levels of Security
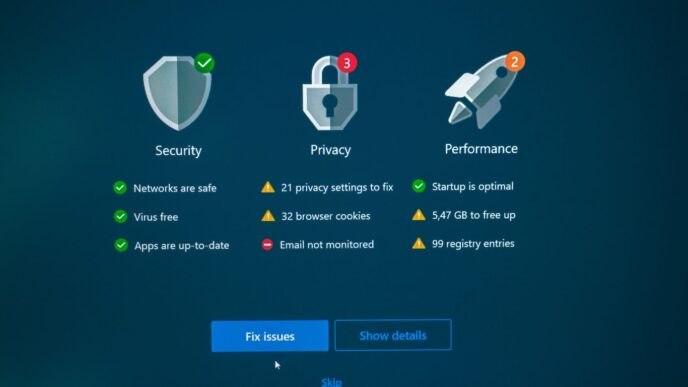
To stay safe online, it is important to understand the different levels of security and how they can protect you. There are three main levels of security: basic, intermediate, and advanced.
Basic security measures include using a strong password and keeping your software up-to-date. Intermediate security measures include using two-factor authentication and a secure browser extension. Advanced security measures include using a virtual private network and encrypting your email.
No matter what level of security you choose, it is important to be aware of the risks involved in using the internet and take steps to protect yourself.
Developing a Secure Cybersecurity Plan
It is no secret that the online world can be dangerous. With all of the news stories about data breaches and cyberattacks, it’s easy to feel like you and your business are at risk. But there is good news: by taking some simple steps, you can develop a cybersecurity plan that will help keep you and your business safe.
Here are some tips for developing a secure cybersecurity plan:
1. Understand the risks. The first step in developing a secure cybersecurity plan is to understand the risks that you and your business face. What types of attacks are you most vulnerable to? What would be the consequences of a successful attack? By understanding the risks, you can better determine what steps need to be taken to protect yourself.
2. Identify your assets. The next step is to identify your assets. What information or systems would be at risk if you were attacked? Make sure to identify both physical and digital assets. Once you know what needs to be protected, you can start to put together the right security measures.
3. Implement security measures. There are many different security measures that you can implement, but not all of them will be right for every business. Some common security measures include firewalls, intrusion detection systems, encryption, and user authentication protocols. Work with a cybersecurity expert to determine which measures make sense for your business and how best to implement them.
4. Train your employees. One of the most important parts of a
Conclusion
We hope this article has given you a better understanding of cybersecurity, why it matters, and how to stay safe online. Cybersecurity is an ever-evolving landscape that requires vigilance from all individuals. By taking the time to learn more about what cybersecurity is and how to protect yourself against cyber threats, you can make sure that your data remains secure both now and in the future. So start brushing up on your knowledge of cybersecurity today!