So, you’ve probably heard a lot of buzz lately about quantum computers and how they might break RSA encryption. It sounds pretty scary, right? Like the internet as we know it is about to crumble. But is it really that simple? We’re going to cut through the noise and talk about what a real RSA crack actually means, what threats are actually out there today, and what you can do to stay safe. It’s not quite as dramatic as some headlines make it seem, but there are definitely things to be aware of.
Key Takeaways
- Don’t get too caught up in the hype about quantum computers breaking RSA right now; current research shows it’s still a long way off for practical, widespread use.
- The RSA algorithm is a public standard, and while it’s widely used, the real cybersecurity threats we face today often involve simpler, low-tech exploits like stolen credentials and social engineering.
- While a quantum computer could theoretically crack RSA, the encryption strength grows massively with key length, making current standards like RSA-2048 still quite robust against today’s technology.
- Organizations should start planning for future quantum risks by looking into post-quantum cryptography and updating their systems, but focus on fixing current security gaps first.
- Claims of a recent RSA crack often involve factoring very small numbers, which is vastly different from breaking the large, complex keys used in modern RSA encryption, making it more of an incremental step than a complete breakthrough.
Understanding the RSA Crack Hype
You might have seen some alarming headlines lately, suggesting that a major breakthrough in quantum computing has effectively broken the RSA encryption we all rely on. It’s enough to make anyone a little nervous about their online security, right? But before we all start panicking and unplugging our routers, let’s take a step back and look at what’s really going on.
Don’t Believe the Quantum Computing Hype
It’s true that quantum computing is a powerful new technology, and it does pose a theoretical future threat to some of our current encryption methods, including RSA. However, the recent news often sensationalizes the actual capabilities. For instance, a recent study demonstrated factoring a 50-bit integer using a mix of quantum and classical methods. While this is a technical step, it’s a world away from cracking the 2048-bit encryption used in most of our daily online activities. Think of it like this:
- Factoring 50-bit integers vs. 2048-bit encryption: The difference in difficulty is astronomical. Factoring a 50-bit number is like trying to pick a simple padlock, while factoring a 2048-bit number is like trying to pick a padlock that has more possible combinations than there are atoms in the universe.
- Incremental steps vs. paradigm shifts: What we’re seeing are small, incremental advances in quantum computing. These are not sudden, massive leaps that render all current encryption obsolete overnight.
- The exponential increase in encryption strength: Each additional bit in an RSA key length dramatically increases the computational power needed to break it. Doubling the key length doesn’t just double the security; it increases it exponentially.
RSA Algorithm: A Public Standard
It’s important to know that the RSA algorithm itself is a public standard, not something owned or controlled by any single company. This means it’s widely available and used across the internet, from securing your online banking to protecting your email. Its widespread adoption is a testament to its effectiveness over many years. However, this also means that any claims about it being
The Quantum Computing Threat Explained
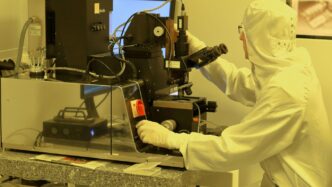
So, let’s talk about quantum computers and how they might mess with RSA encryption. It’s a bit like comparing a regular calculator to a supercomputer, but for math problems that are really, really hard for normal computers.
How Quantum Computing Challenges RSA
RSA’s security relies on how difficult it is for regular computers to factor large numbers. Think of it like trying to find the two specific ingredients that were multiplied together to make a giant number. For today’s computers, that’s practically impossible with the key sizes we use, like 2048 bits. But quantum computers, with their unique way of processing information using ‘qubits’, can tackle certain math problems much faster. This speed difference is the core of the threat.
Shor’s Algorithm: The Primary Threat
There’s a specific quantum algorithm called Shor’s algorithm. If you have a big enough and stable enough quantum computer, this algorithm can factor those large numbers that RSA depends on. It’s not just a little bit faster; it’s exponentially faster. While a regular computer might take billions of years to factor a 2048-bit number, a powerful enough quantum computer running Shor’s algorithm could theoretically do it in hours or days. That’s a game-changer for encryption.
The Quantum Breakthrough: A Closer Look
Now, it’s important to be realistic. We don’t have those super-powerful, error-free quantum computers yet. Today’s quantum computers are often called ‘noisy’ and can only handle a limited number of qubits, and they can only stay stable for tiny fractions of a second. Researchers are making progress, and there are new developments, like machines with more qubits or better stability. However, building a quantum computer capable of breaking RSA-2048 is still a massive engineering challenge. It’s not a matter of if, but when, and the timeline is still very uncertain. Some experts think it’s decades away, while others are more concerned about the near future.
Real-World Implications of an RSA Crack
So, what happens if RSA encryption, the stuff that keeps a lot of our online world safe, actually gets cracked? It’s not just some abstract tech problem; it hits us where we live, digitally speaking.
Harvest Now, Decrypt Later Strategies
Think of it like this: bad actors, maybe even nation-states, are already grabbing up encrypted data they find floating around. They aren’t trying to crack it today. Nope, they’re stashing it away, waiting for the day when they have the super-powerful computers needed to unlock it. This means that sensitive information you sent years ago, or even just last week, could be vulnerable down the road. It’s a bit like someone secretly recording your conversations, planning to listen in much later when they have better hearing aids.
Impact on Banking and Messaging Data
Our financial transactions and private chats are prime targets. If RSA is compromised, your bank account details, transaction histories, and personal messages could all be exposed. Imagine your entire banking history being laid bare, or private conversations becoming public knowledge. This isn’t just about inconvenience; it’s about identity theft, financial ruin, and a complete loss of privacy. The trust we place in digital systems for our most sensitive communications is directly on the line.
Compromised VPNs and Digital Signatures
Virtual Private Networks (VPNs), which many use to stay anonymous online, often rely on RSA for setting up secure connections. If that connection is broken, the whole "private" tunnel collapses, leaving your internet traffic exposed. Beyond that, digital signatures, the electronic equivalent of a handwritten signature used to verify the authenticity of software or documents, also depend on RSA. If these signatures can be faked, you could end up installing malware disguised as a legitimate update, or trusting documents that have been tampered with.
Current State of RSA Encryption
So, where does RSA stand right now? It’s still pretty much everywhere. Think about your everyday internet use – browsing, emailing, online shopping. RSA is often the silent guardian making sure that data stays private during that whole back-and-forth. It’s like the default setting for a lot of the internet’s security.
Widespread Use of RSA-2048
Most websites you visit still rely on RSA, specifically the 2048-bit version, for things like securing your connection when you see that little padlock in your browser. It’s baked into email servers, VPNs, operating systems, and even some of those smart devices in your home. Big names like Google, Facebook, Amazon, and Netflix are still using it. It’s just that common.
Key Lengths and Enhanced Protection
Now, not all RSA is created equal. While RSA-2048 is the most common, some places are already stepping up their game. You’ll find some high-security operations using RSA-4096, which is a longer key and therefore harder to crack. Others are moving to Elliptic Curve Cryptography (ECC), which offers similar security with shorter keys. Signal, for example, uses ECC for its end-to-end encryption, and Cloudflare defaults to it. Even some government sites are looking at ECC.
RSA-2048: Sufficient Protection Through 2030?
So, is RSA-2048 still good enough? Well, the National Institute of Standards and Technology (NIST) has said that 2048-bit keys should be okay for protection until around 2030. It’s not that it’s suddenly weak, but the world of computing is changing fast. The real concern isn’t that RSA-2048 is weak today, but what happens when those future quantum computers become a reality. It’s a bit like having a really strong lock on your door, but knowing that a new type of key is being developed that could open it. For now, keeping up with best practices like regularly rotating your keys is still a solid move.
Preparing Your Infrastructure for Quantum Risks
So, we’ve talked about the quantum threat and why it’s not just science fiction anymore. Now, what do we actually do about it? It’s not like you can just flip a switch and be done. This is about getting our digital house in order before a potential storm hits.
Upgrading Key Sizes and Adopting ECC
One immediate step, though not a permanent fix, is to look at your current encryption. Many systems still rely on RSA-2048, which is a good standard for today’s computers. But as we’ve discussed, quantum computers change the game. While we wait for fully quantum-resistant solutions, beefing up your current encryption is a sensible move. This means looking at larger key sizes for RSA, like 4096-bit keys, which are supported by many modern systems. It’s like putting a stronger lock on your door while you wait for a whole new security system.
Another option is Elliptic Curve Cryptography (ECC). ECC offers similar security levels to RSA but with much smaller key sizes and better performance. Think of it as getting the same protection with a lighter, faster package. It’s still vulnerable to quantum attacks, mind you, but it’s a more efficient option for now and a good stepping stone.
Planning for Post-Quantum Cryptography
This is the big one. The real solution lies in what’s called Post-Quantum Cryptography (PQC). Organizations like NIST have been working on new standards that are designed to be resistant to attacks from both classical and quantum computers. They’ve already released some of these new standards, like Kyber for key exchange and Dilithium for digital signatures. The idea is to start testing these out, perhaps in a hybrid mode where you use both your current encryption and the new PQC methods together. This way, you’re covered no matter what.
It’s a bit like preparing for a major software upgrade. You don’t just install it and hope for the best. You need to plan, test, and make sure everything works smoothly. This transition won’t happen overnight, and it’s going to require careful planning and execution across your entire infrastructure.
Conducting Crypto Audits and Raising Awareness
Before you can upgrade, you need to know what you have. That means doing a thorough audit of your systems. Where is RSA-2048 being used? Is it in your web certificates, your APIs, your devices, your internal communication tools? You need a clear inventory. Once you know where the vulnerabilities lie, you can create a roadmap for upgrading those specific components.
And this isn’t just an IT problem. Everyone needs to be aware of the potential risks. From the folks in finance to the developers writing code, understanding the urgency and the scale of this shift is important. It needs to be part of the long-term planning, not an afterthought. Think of it like a company-wide safety briefing – everyone needs to know the risks and what their role is in staying safe.
Addressing Misconceptions About RSA Cracking
It’s easy to get caught up in the headlines, especially when they talk about "military-grade encryption" being cracked. You might have seen reports about Chinese scientists factoring a 50-bit integer using a mix of quantum and classical methods. This sounds scary, right? But here’s the thing: factoring a 50-bit number is a world away from breaking the 2048-bit encryption that keeps most of our online activity safe. Think of it like this: trying to crack a 50-bit RSA key is like trying to pick a simple padlock, while breaking a 2048-bit key is like trying to break into Fort Knox with just a toothpick. The strength of encryption increases exponentially with key length, making the leap from 50 bits to 2048 bits a monumental one.
Let’s break down some of these common misunderstandings:
- Factoring 50-Bit Integers vs. 2048-Bit Encryption: The recent research demonstrated a method for factoring numbers up to 50 bits. This is a technical achievement, but it’s a far cry from the computational power needed to factor the massive prime numbers used in 2048-bit RSA encryption. Classical computers have been factoring smaller numbers for decades, and quantum computing is still in its early stages for these kinds of tasks. It’s important to remember that the RSA algorithm itself is a public standard, not proprietary technology owned by any single company.
- Incremental Steps vs. Paradigm Shifts: While advancements in quantum computing are happening, the current breakthroughs are best described as incremental steps. They show progress in specific areas, like factoring smaller numbers, but they don’t represent a sudden, paradigm-shifting event that renders all current RSA encryption obsolete overnight. It’s more like building a better tool, not finding a magic key that opens every lock.
- The Exponential Increase in Encryption Strength: The security of RSA encryption relies on the difficulty of factoring large prime numbers. As the key length increases, the number of possible prime factors grows astronomically. For example, moving from 50-bit keys to 2048-bit keys means the number of possibilities increases by a factor that’s incredibly difficult to even comprehend. This exponential growth is why even a significant improvement in factoring smaller numbers doesn’t immediately translate to a threat against longer keys. The National Institute of Standards and Technology (NIST) still believes that 2048-bit RSA keys should provide adequate protection through at least 2030, provided best practices for key management are followed.
It’s also worth noting that focusing solely on the future threat of quantum computing can distract from the very real, low-tech cyber threats that are actively being exploited today. Things like weak passwords, phishing attacks, and unpatched software are still the most common ways systems get compromised. While preparing for post-quantum cryptography is wise, don’t let the hype overshadow the immediate security measures you should be taking.
The Urgency of Post-Quantum Migration

So, we’ve talked about the quantum threat and how it could eventually break RSA. But what does that really mean for us, right now? It means we can’t just sit around and wait for the sky to fall. We need to start planning for a future where our current encryption methods might not be enough. Think of it like getting ready for a big storm; you don’t wait until the rain is pouring to board up the windows. You do it beforehand.
Financial Institutions and Regulatory Pressure
Banks and other financial outfits are really feeling the heat. Regulators are starting to say, "Hey, you need to get this quantum-safe stuff in place." By 2035, many expect financial systems to be fully transitioned. This isn’t just about avoiding fines; it’s about keeping customer data, like credit card numbers and transaction histories, safe from future decryption. Imagine all those secure online banking sessions being readable years down the line – that’s a massive problem.
The Clock is Ticking for Cryptographic Guarantees
It’s easy to think quantum computers are still science fiction, but the progress is real. Researchers are making big leaps, and while we don’t know exactly when a powerful enough quantum computer will exist, we know it’s coming. The scary part is that data encrypted today could be stored by attackers and decrypted later, once they have the right tools. This "harvest now, decrypt later" strategy means even data that seems safe now could be at risk in the future. We’re talking about potentially years of sensitive information being exposed.
Is Post-Quantum Cryptography the Next Y2K?
Some folks are comparing this to the Y2K scare back in the day. Remember how everyone was worried computers would stop working at midnight on January 1, 2000? It was a big deal, and a lot of work went into fixing it. This quantum migration might be even bigger. It’s not just about updating a few lines of code; it’s about potentially changing the fundamental ways we secure almost everything online – from websites and emails to digital signatures and VPNs. Getting this right will take time, coordination, and a serious commitment from everyone involved, from governments to individual companies.
So, What’s the Real Story?
Look, the idea of quantum computers breaking RSA encryption sounds pretty scary, and honestly, the headlines can make it seem like the sky is falling. But the truth is a bit more complicated. While researchers are making progress, the kind of quantum computer needed to actually crack today’s RSA encryption is still a long way off. We’re talking about systems that are massive, expensive, and not yet built. Instead of worrying about a future threat that might not happen for years, it’s way more important to focus on the security problems we have right now. Things like weak passwords, not using multi-factor authentication, and just generally not keeping track of who has access to what – those are the things hackers are exploiting today. RSA itself offers ways to make keys longer, which helps for now. Plus, there are new types of encryption being developed, called post-quantum cryptography, that will be ready when we need them. So, while it’s good to be aware of what’s coming, don’t lose sleep over quantum computers just yet. Let’s fix the basic security stuff first.
Frequently Asked Questions
Is RSA encryption really broken by quantum computers right now?
Not yet. While scientists are making progress, the quantum computers needed to break today’s RSA encryption are still a long way off. Think of it like this: breaking a 2048-bit RSA code would take a super-powerful quantum computer many, many years, far longer than it takes to crack much simpler codes. Current quantum computers are not even close to being powerful enough.
What’s the big deal about quantum computers and RSA?
RSA encryption works by making it incredibly hard for regular computers to figure out very large numbers. Quantum computers, however, are a different kind of machine. They have a special way of working that could, in the future, make it much easier to solve the math problems that RSA relies on, potentially making current encryption methods unsafe.
If RSA isn’t broken now, why should I worry?
Some bad actors might be saving encrypted data they steal today. They’re hoping that in the future, when quantum computers are powerful enough, they can go back and unlock that data. This is called a ‘harvest now, decrypt later’ strategy. So, even though the threat isn’t immediate, preparing for it is important.
Are there ways to make RSA stronger against future threats?
Yes! One way is to use longer ‘keys’ for RSA encryption. While 2048-bit keys are common, using 4096-bit keys makes the code much harder to crack. Another approach is to switch to newer types of encryption that are designed to be safe from quantum computers, like those being developed by organizations like NIST.
What are the real cybersecurity dangers I should focus on today?
Instead of worrying too much about future quantum threats, it’s more important to focus on current, simpler cyberattacks. These include things like weak passwords, not using multi-factor authentication (like a code sent to your phone), and falling for scams that trick you into giving away information. These are the methods hackers use successfully right now.
How can my organization get ready for potential quantum computer threats?
Organizations should start by checking where they use RSA encryption and plan to upgrade to stronger or quantum-resistant methods. It’s also a good idea to train employees about cybersecurity risks and stay updated on new encryption standards. Think of it like getting your house ready for a storm that might happen years from now – you do the preparations now to be safe later.