Computer security, firewall, or just information technology security is basically the protection of networks and computer systems from unauthorized access, data loss or damage, and from the disruption or misuse of their services. The ultimate aim of these systems is to hinder or prevent hackers and other cyber-criminals from carrying out their nefarious plans on your computer and/or its peripherals. Most modern-day computers are networked to many other devices that are connected, either directly or indirectly, to a wide array of other devices. All of this creates a situation where the more a hacker can manipulate or access, the easier it would be for him or her to carry out his or her agenda.
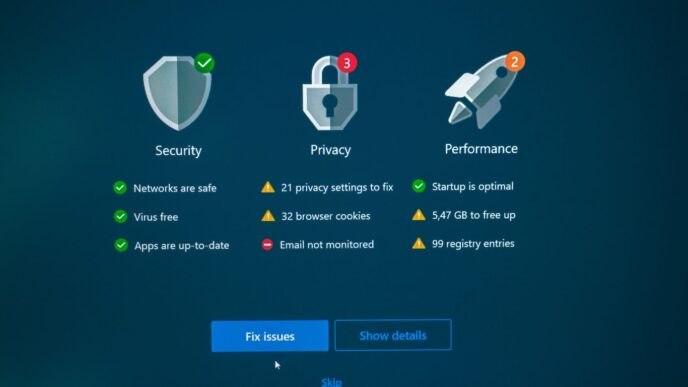
One of the best ways to enhance information technology security at your company is through an information technology security management program (ITSP). An ITSP is a specialized security suite consisting of various computer network security measures, including intrusion detection, tracking, and reporting. By improving the overall security of your company’s computer system, an ITSP will help you : (a) Reduce the number of system attacks and vulnerabilities, (b) Minimize the damage and loss suffered by a compromised computer network, and (c) Minimize the downtime that a badly damaged or corrupted computer system would cause. While an ITSP might cost some money upfront, it is a good investment in protecting the future of your business. An ITSP will help you identify threats early, resolve threats after they have taken hold, and prevent vulnerabilities from becoming vulnerabilities again. They will also help to ensure that all employees and systems are properly updated with the most current threat protection definitions.
As a business owner or manager, it is of vital importance that you understand the latest developments in the field of cyber security so that you can take the necessary steps to protect your computer systems, network, and information. Today, there are many different types of malware, phishing attacks, and other malicious software programs that are being developed on an almost daily basis. Because of this, it is important for businesses to implement information technology security measures so that they can protect themselves against unauthorized access, data loss, and electronic sabotage.

When it comes to information technology security, you must work closely with the people who will be accessing your network, particularly those who have access to data that needs to be secured. It is important for these individuals to be trained in the proper use of the anti-malware, firewall, and anti-phishing software that is available. In addition to these individuals, you should also train your supervisors so that they know how to address the different issues that may arise as a result of a recent cyber security attack. This way, you can rest assured that your company’s network is as safe and secure as possible at all times.
Information technology security measures can include a variety of different methods. There are measures that can be taken against unauthorized access to computer networks. For example, you can install firewalls that are designed to prevent hackers from getting into your system. You can also employ various types of security software programs that can screen the incoming data so that it is not only safe, but it is also highly confidential. You can also set up physical barriers at the entrances to your network or your building so that anyone entering must be authorized by you and/or a senior administrator.
Cybersecurity specialists can help you keep your company’s network safe and secure so that you can run your business uninterrupted. Because cyber security specialists are readily available 24 hours a day, seven days a week, it is vital for businesses to hire these specialists. The more security specialists you have on staff, the less chance there is of an information technology security breach. This way, your company can protect itself from potential data breaches even while you are conducting your normal operations.