Introduction:
In an era dominated by digital connectivity and technological advancements, the importance of cybersecurity has never been more critical. As businesses, governments, and individuals continue to embrace the digital frontier, the need to protect sensitive information from cyber threats becomes paramount. This article explores the significance of cybersecurity, the evolving threat landscape, and the measures taken to secure the digital realm.
The Landscape of Cyber Threats:
- Sophisticated Cyber Attacks: Cyber threats have evolved from simple viruses to highly sophisticated and targeted attacks. Advanced Persistent Threats (APTs), ransomware, and phishing attacks are just a few examples of the tactics employed by cybercriminals to exploit vulnerabilities and compromise digital systems.
- Data Breaches: The increasing frequency of data breaches highlights the vulnerability of digital systems. Cybercriminals often target databases containing sensitive information, such as personal data, financial records, and intellectual property. The aftermath of a data breach can have severe consequences for individuals and organizations alike.
The Imperative of Cybersecurity:
- Protection of Sensitive Information: Cybersecurity is fundamentally about protecting sensitive information from unauthorized access, disclosure, alteration, and destruction. This includes personal data, financial information, trade secrets, and any data critical to the functioning of organizations and individuals.
- Preserving Privacy: As digital interactions become integral to daily life, preserving privacy is a key component of cybersecurity. Individuals entrust various platforms with their personal information, and cybersecurity measures ensure that this information remains confidential and is not misused.
Key Components of Cybersecurity:
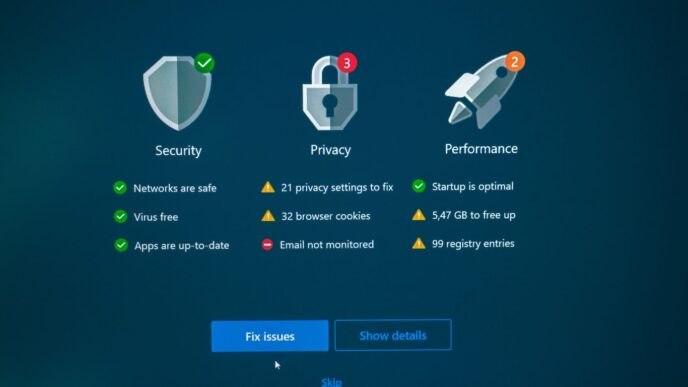
- Firewalls and Intrusion Detection Systems: Firewalls act as barriers between a secure internal network and external networks, monitoring and controlling incoming and outgoing network traffic. Intrusion Detection Systems (IDS) identify and respond to suspicious activities that may indicate a security breach.
- Secure Authentication Protocols: Strong authentication measures, such as two-factor authentication (2FA) and biometric authentication, add an additional layer of security to prevent unauthorized access to accounts and systems.
- Regular Software Updates and Patch Management: Keeping software and systems up-to-date is crucial for closing potential security vulnerabilities. Regular updates and patches provided by software vendors address known security issues and protect against emerging threats.
- Employee Training and Awareness: Human error is a significant factor in cybersecurity incidents. Training employees to recognize phishing attempts, follow secure password practices, and adhere to cybersecurity policies is essential in building a resilient defense against cyber threats.
Cybersecurity in the Business Landscape:
- Protection of Intellectual Property: For businesses, protecting intellectual property is a top priority. Cybersecurity measures safeguard proprietary information, trade secrets, and research and development efforts from theft or unauthorized access.
- Maintaining Customer Trust: A robust cybersecurity framework is crucial for maintaining customer trust. Businesses that demonstrate a commitment to protecting customer data not only comply with regulations but also foster a sense of security and trust among their clientele.
Evolving Technologies in Cybersecurity:
- Artificial Intelligence (AI) and Machine Learning (ML): AI and ML are being increasingly integrated into cybersecurity systems to analyze patterns, detect anomalies, and respond to threats in real-time. These technologies enhance the efficiency of cybersecurity measures, allowing for proactive threat detection and mitigation.
- Blockchain Technology: Blockchain, known for its use in cryptocurrencies, is gaining traction in cybersecurity. Its decentralized and tamper-proof nature makes it a potential solution for securing sensitive data and preventing unauthorized alterations.
Global Collaboration in Cybersecurity:
- International Cooperation: Given the borderless nature of cyber threats, international cooperation is essential. Countries and organizations collaborate to share threat intelligence, establish cybersecurity standards, and coordinate responses to cyber incidents.
- Regulatory Frameworks: Governments worldwide are implementing regulatory frameworks to ensure that businesses adhere to cybersecurity standards. Compliance with regulations not only mitigates risks but also fosters a culture of cybersecurity awareness and accountability.
Conclusion:
As the digital landscape continues to evolve, cybersecurity stands as a formidable shield against the ever-growing array of cyber threats. It is not merely a technical necessity but a critical component in preserving the integrity of personal, organizational, and global digital ecosystems. The imperative of cybersecurity is a shared responsibility that requires continuous vigilance, technological innovation, and a collaborative approach to safeguard the digital future. In a world where connectivity is the norm, the strength of our digital defenses will determine our resilience in the face of cyber challenges.