In the digital age, our lives are intricately entwined with the internet. From social interactions and online shopping to remote work and banking, we rely on the web for countless activities. However, this dependency brings a plethora of risks, making it crucial to understand and mitigate online threats effectively. This guide aims to equip you with knowledge and strategies to safeguard your digital presence.
Understanding Online Risks
Types of Online Risks
- Phishing Attacks: These involve fraudulent attempts to obtain sensitive information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity. Phishing emails and websites are often designed to look legitimate, making it easy for unsuspecting users to fall prey.
- Malware: Malicious software, known as malware, includes viruses, worms, Trojan horses, ransomware, and spyware. These programs can damage or disable computers, steal data, and cause other forms of havoc.
- Identity Theft: Cybercriminals can steal personal information to commit fraud, such as making unauthorized purchases or opening new accounts in your name. Identity theft can have long-lasting impacts on your financial health and personal reputation.
- Data Breaches: Unauthorized access to confidential information stored by companies can expose sensitive data to cybercriminals. This can lead to financial loss, reputational damage, and legal consequences for the affected organizations.
- Social Engineering: This involves manipulating individuals into divulging confidential information or performing actions that compromise security. Techniques include pretexting, baiting, and tailgating.
The Impact of Online Risks
The consequences of falling victim to online risks can be severe. Financial loss, emotional distress, and professional setbacks are common repercussions. Moreover, recovering from a cyberattack can be time-consuming and costly. Therefore, proactive measures are essential to minimize exposure to online threats.
Mitigating Online Risks
Best Practices for Individuals
- Strong Passwords: Use complex passwords that combine letters, numbers, and special characters. Avoid using the same password across multiple accounts and consider using a password manager for added security.
- Two-Factor Authentication (2FA): Enable 2FA wherever possible. This adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
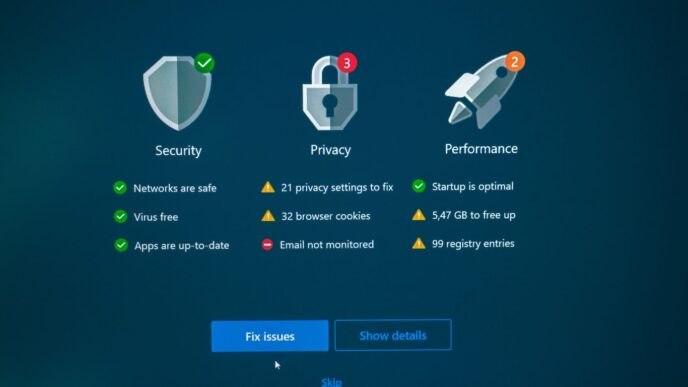
- Regular Software Updates: Keep your operating system, antivirus software, and all applications up to date. Updates often include patches for security vulnerabilities that cybercriminals can exploit.
- Be Wary of Suspicious Links and Emails: Do not click on links or download attachments from unknown sources. Verify the authenticity of emails by checking the sender’s address and looking for signs of phishing, such as spelling errors or urgent requests for personal information.
- Secure Your Devices: Use antivirus software and firewalls to protect your devices. Ensure that your Wi-Fi network is secured with a strong password and encryption.
Best Practices for Organizations
- Employee Training: Conduct regular training sessions to educate employees about online risks and safe practices. Phishing simulations can help raise awareness and improve response to real threats.
- Data Encryption: Encrypt sensitive data both in transit and at rest. This ensures that even if data is intercepted or accessed without authorization, it remains unreadable and unusable.
- Access Controls: Implement strict access controls to restrict who can view or modify sensitive information. Use the principle of least privilege, granting users the minimum level of access necessary for their role.
- Incident Response Plan: Develop and maintain an incident response plan to quickly address and mitigate the impact of a cyberattack. This should include steps for communication, containment, eradication, and recovery.
- Regular Security Audits: Conduct periodic security assessments to identify and address vulnerabilities in your systems and processes. This helps ensure that your defenses remain robust and up to date.
Reduce Exposure to Cyber Threats
Understanding and mitigating online risks is vital in today’s interconnected world. By adopting best practices and staying vigilant, both individuals and organizations can significantly reduce their exposure to cyber threats. Remember, cybersecurity is an ongoing process, and staying informed about emerging risks and technologies is key to maintaining a secure digital presence.