Cybercrime is becoming more sophisticated and prevalent than ever before, with hackers constantly finding new ways to breach digital security. With businesses and individuals alike falling victim to cyberattacks, it’s essential that you are equipped with the knowledge necessary to protect yourself from potential threats. In this blog post, we’ll explore all you need to know about cyberattacks and provide practical tips on how you can safeguard your online presence against them.
What is a Cyber Attack?
A cyberattack is a type of security breach that involves the unauthorized use of computer networks and/or devices to access, disrupt, or steal data. Cyberattacks can be carried out by individuals, groups, or even governments and can target individuals, organizations, or entire infrastructure systems.
There are many different types of cyberattacks, but some of the most common include malware infections, phishing scams, denial-of-service attacks, and SQL injection attacks. Malware is a type of malicious software that can infect computers and devices in order to damage or disable them or gain access to sensitive information. Phishing scams are attempts to trick users into revealing confidential information (such as passwords or credit card numbers) by masquerading as a trustworthy entity in an email or other communication. Denial-of-service attacks seek to render websites or other online services unavailable by flooding them with traffic from multiple computers or devices. SQL injection attacks exploit vulnerabilities in web applications in order to inject malicious code into the database underlying the app (this can allow attackers to gain access to sensitive data).
Cyberattacks can have serious consequences for individuals and organizations alike. In addition to causing financial damage (from things like lost productivity or data recovery costs), they can also lead to the loss of sensitive data, reputational damage, and even physical harm. That’s why it’s important for everyone—both individuals and organizations—to be aware of the dangers of cyberattacks and take steps to
Types of Cyber Attacks
There are many different types of cyberattacks, and each one can be devastating to businesses and individuals alike. Here are some of the most common types of cyberattacks:
1. Malware Attacks: Malware is a type of malicious software that is designed to damage or disable computers. It can be installed on a computer without the user’s knowledge or permission and can be used to steal sensitive information, destroy data, or take control of the victim’s machine.
2. Phishing Attacks: Phishing is a type of social engineering attack in which the attacker attempts to trick the victim into disclosing sensitive information or downloading malware. Phishing emails often look like they come from a legitimate company or individual and may contain links or attachments that lead to malicious websites or downloads.
3. Denial-of-Service (DoS) Attacks: A DoS attack is an attempt to make a computer or network resource unavailable to users. This can be done by overwhelming the target with traffic, flooding it with requests until it crashes, or exploiting vulnerabilities in order to disable it.
4. SQL Injection Attacks: SQL injection attacks take advantage of vulnerabilities in web applications in order to inject malicious code into the database that powers the application. This allows attackers to gain access to sensitive data, modify it, or delete it entirely.
5. Password Attacks: Password attacks are attempts to guess or brute force passwords in order to gain access to accounts or systems.
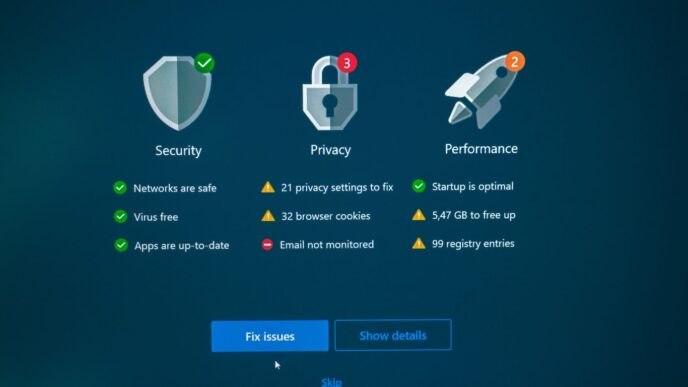
Common Signs of a Cyber Attack
When it comes to cybercrime, there is no one-size-fits-all solution. However, there are some common signs that can indicate that your organization is under attack. These include:
1. Unexpected or unusual activity on your network This could include new or unexpected devices accessing the network, strange traffic patterns, or unusual login activity.
2. Suspicious emails or other communications from unknown senders Be wary of any unsolicited emails, especially those with attachments or links.
3. Changes to critical files or systems without explanation This could be anything from changes in permissions to new files appearing in sensitive locations.
4. Poor performance from critical systems or applications A cyberattack can often overload systems and cause them to run slowly or crash completely.
5. Unexpected popup windows or messages appearing on your screen This is often a sign of malicious software being installed on your computer without your knowledge.
If you notice any of these signs, it’s important to take action immediately. The longer you wait, the more damage the attackers can do and the harder it will be to recover from the attack.
How to Protect Yourself from a Cyber Attack
Cyberattacks are becoming increasingly common, and they can be devastating. Here are some tips to help protect yourself from a cyberattack:
1. Keep your software up to date. One of the best ways to protect yourself from a cyberattack is to make sure that all of your software is up-to-date. Cybercriminals often exploit vulnerabilities in outdated software, so keeping your software up-to-date is one of the best things you can do to protect yourself.
2. Use strong passwords and two-factor authentication. Another important way to protect yourself from a cyberattack is to use strong passwords and two-factor authentication whenever possible. Strong passwords are difficult for hackers to guess, and two-factor authentication adds an extra layer of security by requiring you to enter a code from your mobile phone in addition to your password.
3. Be careful what you click on. One of the most common ways that cybercriminals try to infect computers with malware is by sending email attachments or links that contain malicious code. Be very careful about what you click on, even if it comes from someone you know, and only open email attachments or click on links from trusted sources.
4. Back up your data regularly. In the event that you do become the victim of a cyberattack, it’s important to have a backup of your data so that you can restore your files if necessary. Backing up your data regularly is the best way to ensure that you have a copy in case of
Best Practices for Keeping Your Data and Systems Secure
As the world becomes increasingly digital, so do the opportunities for criminals to commit cybercrimes. Here are some best practices for keeping your data and systems secure:
1. Keep your software up to date. Outdated software is one of the biggest security vulnerabilities. Be sure to install updates as soon as they’re available.
2. Use strong passwords and never reuse them. Passwords should be at least eight characters long and include a mix of letters, numbers, and symbols.
3. Encrypt sensitive data. Encryption is one of the best ways to protect data from being accessed by unauthorized individuals.
4. Store backups off-site. In the event that your data is compromised, having backups stored off-site will ensure that you can still access your critical information.
5. Implement security measures such as firewalls and intrusion detection systems. These tools can help prevent cyberattacks from happening in the first place.
Conclusion
Cybercrime is an ever-growing threat, and the onus lies upon us as individuals to protect ourselves from falling victim to it. We must remain vigilant in order to ensure we don’t fall prey to cybercriminals. By taking some simple steps such as using strong passwords, avoiding clicking unknown links, and keeping our software up-to-date, we can reduce the risk of being a target for malicious attacks online. Remember, cybersecurity is everyone’s responsibility!