Introduction:
In today’s interconnected world, where technology plays a central role in our lives, it’s crucial to understand the impact of cyberattacks. These malicious acts can wreak havoc on individuals, organizations, and even nations. we will explore these impactful incidents and shed light on their implications. Let’s dive in!
The Top 20 Cyber Attacks That Shook the World
- Stuxnet:
Originating in 2010, Stuxnet is considered the world’s first digital weapon. It targeted Iran’s nuclear program, specifically its uranium enrichment centrifuges. Stuxnet showcased the power of cyberwarfare and its potential to disrupt critical infrastructure. - WannaCry:
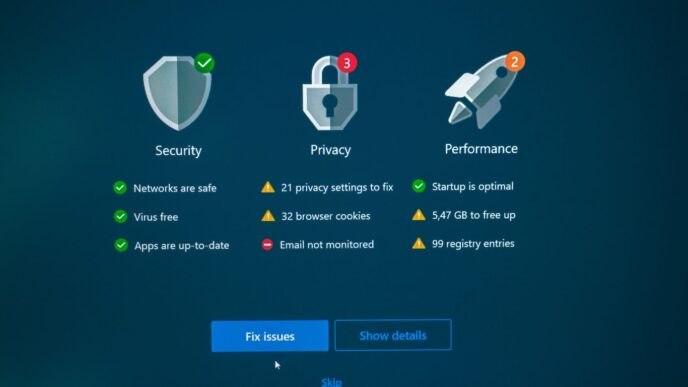
In 2017, the WannaCry ransomware attack infected hundreds of thousands of computers worldwide. Exploiting a vulnerability in Windows systems, it encrypted files and demanded a ransom in Bitcoin. This attack highlighted the importance of timely software updates and cybersecurity measures. - Equifax Data Breach:
One of the most significant data breaches in history occurred in 2017 when Equifax, a leading credit reporting agency, was hacked. Approximately 147 million people had their personal information exposed, emphasizing the need for robust data protection practices. - NotPetya:
Initially disguised as ransomware, NotPetya emerged in 2017 and targeted Ukrainian businesses. However, it quickly spread globally, affecting multinational corporations. The attack caused billions of dollars in damages, illustrating the potential collateral damage of cyberwarfare. - SolarWinds Supply Chain Attack:
Discovered in 2020, the SolarWinds attack compromised numerous organizations, including government agencies. Hackers infiltrated SolarWinds’ software update process, enabling them to distribute malicious updates and gain access to sensitive data. - Sony Pictures Hack:
In 2014, a group called Guardians of Peace attacked Sony Pictures, leaking confidential data, unreleased movies, and personal emails. The attack revealed the vulnerability of organizations and the importance of robust cybersecurity protocols. - Yahoo Data Breach:
Yahoo experienced two massive data breaches in 2013 and 2014, affecting billions of users. The breaches compromised personal information, highlighting the significance of strong passwords, two-factor authentication, and cautious online behavior. - Target point-of-Sale breach:
In 2013, cybercriminals infiltrated Target’s point-of-sale systems, stealing credit and debit card data from approximately 40 million customers. This incident underlined the importance of secure payment processing and the need for constant vigilance against emerging threats. - Heartbleed:
Heartbleed, discovered in 2014, exploited a vulnerability in OpenSSL, a widely used cryptographic library. The bug allowed hackers to access sensitive information, such as passwords and encryption keys. Heartbleed highlighted the need for prompt security patching and vulnerability management. - Mirai Botnet:
In 2016, the Mirai botnet harnessed vulnerable Internet of Things (IoT) devices to launch massive distributed denial-of-service (DDoS) attacks. This event exposed the risks associated with poorly secured IoT devices and the importance of device-level security measures. - Petya/NotPetya Ransomware:
In 2016, the Petya ransomware infected systems worldwide, encrypting hard drives and demanding ransom. This attack underscored the significance of regular data backups and robust cybersecurity practices to mitigate the impact of ransomware attacks. - Ashley Madison Data Breach:
Ashley Madison, a dating website for extramarital affairs, fell victim to a data breach in 2015. The incident exposed sensitive user information, highlighting the need for stringent data protection and privacy measures. - Google-China Cyber Espionage:
In 2009, Google reported a series of cyberattacks originating from China, targeting human rights activists and stealing intellectual property. This incident prompted discussions on state-sponsored cyber espionage and the significance of international cybersecurity cooperation. - Anthem Data Breach:
In 2015, Anthem, one of the largest health insurance companies in the U.S., suffered a data breach affecting nearly 80 million individuals. The incident emphasized the importance of safeguarding personal healthcare information and the potential consequences of compromised medical data. - CryptoLocker Ransomware:
CryptoLocker, first observed in 2013, infected computers and encrypted files, demanding a ransom for their release. This attack highlighted the risks associated with opening suspicious email attachments and the importance of robust cybersecurity measures. - Operation Aurora:
Operation Aurora, identified in 2009, targeted several major companies, including Google, Adobe, and Juniper Networks. The attack exploited vulnerabilities in Internet Explorer, emphasizing the significance of browser security updates and proactive threat mitigation. - The Shadow Brokers:
In 2016, a hacker group known as The Shadow Brokers leaked a collection of cyberweapons, allegedly stolen from the National Security Agency (NSA). This event raised concerns about the potential repercussions of government-developed hacking tools falling into the wrong hands. - CIA Vault 7 Leaks:
In 2017, WikiLeaks published the Vault 7 leaks, which exposed the CIA’s hacking capabilities. The leaks highlighted the scale of government surveillance and the importance of robust encryption and privacy measures. - Operation Shady Rat:
Operation Shady RAT, discovered in 2011, targeted numerous organizations worldwide, including governments, defense contractors, and technology companies. The attack emphasized the significance of advanced persistent threats (APTs) and the need for continuous monitoring and incident response. - The Great Firewall of China:
China’s Great Firewall refers to the country’s extensive internet censorship and surveillance mechanisms. Understanding this phenomenon is crucial for comprehending the impact of state-controlled cyberspace and the importance of digital freedoms.