Lately, it feels like every other day there’s news about some new cyber threat making headlines. It’s getting pretty wild out there. A big part of this is how attackers are getting smarter about breaking into networks, and a common weak spot they’re hitting are firewalls. You know, those devices supposed to be our digital gatekeepers. This article is going to look at how these firewalls, which are supposed to keep us safe, are actually getting hacked and what that means for everyone.
Key Takeaways
- Firewalls are increasingly becoming targets for cyber attackers because they sit at the edge of networks and offer a direct path for deeper intrusion.
- Specific brands like Fortinet FortiGate and Cisco firewalls have seen a rise in attacks, often exploiting known vulnerabilities or weak configurations.
- Attackers are using various methods, including exploiting management plane flaws and even zero-day vulnerabilities, to gain unauthorized access.
- A compromised firewall can give attackers broad access, enabling them to move freely within a network, steal data, and deploy ransomware.
- To protect against these threats, organizations need strong logging, regular vulnerability management that goes beyond simple scores, and thorough security hardening practices.
Exploiting Firewall Vulnerabilities: A Growing Threat
It feels like every week there’s a new headline about a cyberattack, and increasingly, the entry point is something you’d think would be a fortress: the firewall. These devices sit right at the edge of our networks, acting as the first line of defense. But it turns out, they’re not always as impenetrable as we’d like to believe. Attackers are getting smarter, and they’re finding ways around these digital gatekeepers.
Understanding the Appeal of Perimeter Devices
Firewalls, and other network edge devices, are like the front doors to your digital house. They’re designed to control who and what gets in and out. Because they have such a central role, they offer attackers a really attractive position. If you can get past the firewall, you’ve essentially bypassed a major security hurdle. This makes them prime real estate for anyone looking to cause trouble online. It’s not just about getting in; it’s about getting in with a privileged view of everything happening inside. This is why network edge devices are such a hot target.
The Evolving Tactics of Threat Actors
Gone are the days when attackers just brute-forced their way in. Now, they’re using more sophisticated methods. They’re looking for specific weaknesses, like unpatched software or misconfigurations. Sometimes, they’re even finding flaws that haven’t been publicly disclosed yet – these are called zero-days. It’s a constant cat-and-mouse game, with attackers always trying to stay one step ahead of the defenders. They’re not just randomly poking around; they’re actively researching and developing ways to exploit these devices.
Why Firewalls Are Prime Targets
So, why are firewalls such a big deal for attackers? Well, think about it. A compromised firewall can give an attacker a lot of power. They can see a huge amount of network traffic, which is great for gathering intelligence or planning further attacks. Plus, many firewalls have administrative access, meaning attackers can potentially control network settings, create new user accounts, or even disable security features. It’s a gateway to the entire network. In fact, a staggering 90% of ransomware attacks use firewall vulnerabilities as their entry point, which really puts things into perspective.
Fortinet FortiGate Devices Under Siege
It seems like Fortinet FortiGate devices are really catching it lately. We’re seeing a lot of automated attacks aimed squarely at these firewalls, and honestly, it’s a bit concerning. These aren’t just random hits; attackers are actively trying to get in and mess with things. They’re using these firewalls as a way to get a foot in the door to the rest of a company’s network.
Abuse of FortiGate Appliances as Entry Points
So, how are they doing it? Well, attackers are finding ways to exploit security holes, some of them pretty new, or just plain weak passwords and settings. Once they get in, they can grab configuration files. These files are like a treasure map for hackers, often containing credentials for important services, like Active Directory or LDAP. This gives them a much better idea of how the network is set up and where to go next. It’s like finding the keys to the kingdom hidden in the firewall’s manual.
Exploiting Weak Credentials and Configuration Files
We’ve seen cases where hackers create new admin accounts, like one called "support," and then set up rules that let them move around the network without any checks. They’ll even pop back in later to make sure their access is still good, kind of like an initial access broker setting up shop. Then, they grab those configuration files. If they can decrypt the service account passwords inside, they can use those to log into the main network and start enrolling fake computers. It’s a pretty slick, if scary, way to get deeper into a system. This is happening with FortiCloud single sign-on vulnerabilities too.
Targeting Critical Sectors: Healthcare and Government
What’s really worrying is who these attacks are hitting. Reports show that healthcare, government agencies, and companies that manage IT for others are being singled out. These are places that hold sensitive data and provide important services. When their firewalls are compromised, the fallout can be pretty severe. In some instances, attackers have moved from the firewall to installing remote access tools and even downloading malware to steal data. It’s a cascade effect, and it all starts with getting past that first line of defense, the firewall. These automated attacks are a serious problem.
Cisco Firewalls and SD-WANs: A Cascade of Exploits
It seems like every week there’s a new security alert about Cisco gear. Lately, it’s been a real flood of issues hitting their firewalls and SD-WAN systems. We’re talking about a bunch of vulnerabilities, and the scary part is that many of them are already being actively used by attackers. It’s not just a few minor bugs either; some of these are pretty serious.
The fact that attackers are getting their hands on these flaws before Cisco or security researchers even know about them is a major problem. This has been happening with some of the SD-WAN vulnerabilities, where bad actors were exploiting them for years before anyone caught on. It’s like leaving your front door wide open and not realizing it for a long time.
Here’s a quick look at what’s been going on:
- Actively Exploited Vulnerabilities: Cisco has disclosed nine vulnerabilities in their firewalls and SD-WAN products recently. Out of these, five have already been confirmed as being used in real-world attacks. This is a pretty high number, and it means a lot of organizations are potentially at risk right now.
- Zero-Day Exploitation: Some of the most concerning issues involve zero-day vulnerabilities in Cisco SD-WANs. These are flaws that attackers know about and use, but the vendor and the public don’t. We’ve seen cases where these were exploited for years before being discovered. This gives attackers a massive advantage.
- Ransomware Campaigns: It’s not just about getting access; these vulnerabilities are also being used in serious attacks like ransomware. The Interlock ransomware group, for example, has been using a zero-day flaw in Cisco’s firewall management software since January. They’re targeting sectors like healthcare and government, which can cause huge disruptions.
It’s a tough situation because these devices are so important. Compromising a firewall or an SD-WAN management system means attackers can get a lot of control over your network. They can see everything, change how traffic flows, and basically get administrative trust over a large part of your infrastructure. It’s a goldmine for them. You can find more details on some of these Cisco SD-WAN vulnerabilities and the ongoing risks they present. The Cybersecurity and Infrastructure Security Agency (CISA) has also flagged some of these as actively exploited, which is a big deal. You can check out CISA’s alerts on exploited Cisco vulnerabilities for more information.
Attack Vectors Leading to a Firewall Hacked
So, how exactly do these supposedly secure firewalls end up getting compromised? It’s not usually a single, dramatic event, but more like a series of steps that attackers exploit. They’re getting pretty clever, and sometimes it feels like they’re just a step ahead.
Leveraging Pre-Authentication Management Plane Flaws
One of the scariest ways attackers get in is by finding weaknesses in the firewall’s management interface before they even need to log in. Think of it like finding a back door that’s unlocked, even though the front door is heavily guarded. These flaws, often in the management plane, let them bypass authentication checks entirely. This is a big deal because it means they can potentially gain access and start messing with settings without anyone knowing. It’s like someone walking into your house and rearranging the furniture before you even realize they’re there. Some groups are even using AI to speed this up, creating an "AI-powered assembly line for cybercrime" [b3f4].
Automated Attacks Creating Rogue Accounts
Once attackers find a way in, or even as part of the initial breach, they often set up automated processes. These aren’t slow, manual hacks. They’re fast, efficient, and designed to create new accounts that shouldn’t exist. For example, attackers have been seen creating administrator accounts named "support" on FortiGate devices. They then use these accounts to set up new firewall rules that give them free rein across the network. It’s a way to establish a persistent foothold, making sure they can get back in later. They might also steal configuration files, which can contain sensitive credentials for other systems, like Active Directory. This is a huge problem, especially for places like healthcare and government organizations that rely heavily on these devices for security.
Exploiting Single Sign-On Vulnerabilities
Single Sign-On (SSO) is supposed to make things easier and more secure, but it can also become a weak point. Attackers are specifically targeting SSO features on firewalls. If they can compromise the SSO mechanism, they can potentially gain access to multiple systems or create accounts with broad permissions. In some cases, attackers have exploited SSO flaws to create accounts with VPN access and then immediately export firewall configurations. This whole process can happen in mere seconds, showing just how automated and rapid these attacks can be. It really highlights the need to secure every part of the authentication process, not just the main login screen. The Akira ransomware group, for instance, has been actively exploiting SonicWall vulnerabilities that have been unpatched for a year [f722], showing how persistent threats can be.
Consequences of a Compromised Firewall
So, what happens when attackers actually get past your firewall? It’s not pretty, folks. Think of your firewall as the main gatekeeper for your entire network. If someone bad gets through that gate, they’ve basically got the keys to the kingdom.
Gaining Privileged Access and Broad Visibility
Once an attacker breaches the firewall, they often gain administrative privileges. This means they can see and do pretty much anything on your network. They can access sensitive data, change configurations, and even disable security measures. It’s like giving a burglar the master keys to your house, along with the blueprints. They can see where all the valuables are stored and how to get to them easily. This level of access is a huge win for them, allowing them to plan their next moves with detailed knowledge of your infrastructure. It’s a stark reminder of why securing these perimeter devices is so important, especially when you consider the human element in firewall vulnerabilities.
Lateral Movement and Deeper Network Compromises
Getting into the firewall is just the first step. From there, attackers use that privileged access to move deeper into your network. This is called lateral movement. They hop from one system to another, looking for more valuable targets like servers with customer data or financial information. They might exploit weak passwords on internal systems or use legitimate tools to blend in. This process can be slow and stealthy, making it hard to detect until significant damage is done. It’s a cascade effect; one breach leads to another, and before you know it, your entire network is compromised. This is why a Zero Trust approach is so vital, constantly verifying every access attempt.
Data Exfiltration and Extortion Tactics
With broad access and the ability to move freely, attackers can now steal your sensitive data. This could be customer lists, financial records, intellectual property, or anything else they can sell or use for further attacks. Sometimes, they don’t just steal it; they encrypt it and demand a ransom to get it back. This is ransomware, and it can cripple a business. They might also threaten to release stolen data publicly if the ransom isn’t paid, adding a layer of public embarrassment and reputational damage to the financial hit. The goal is often financial gain, and a compromised firewall is a direct path to achieving that.
Mitigating the Risk of a Firewall Hacked
So, we’ve talked about how firewalls can get compromised, and it’s not a pretty picture. The good news is, it’s not all doom and gloom. There are definitely steps you can take to make your network a much tougher target. It really comes down to being proactive and not just waiting for something bad to happen.
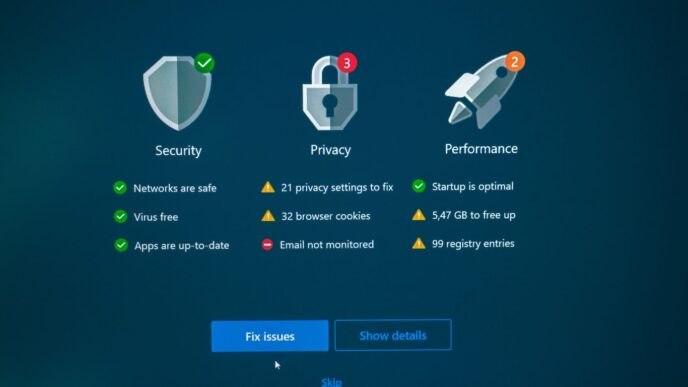
The Importance of Adequate Logging and SIEM Integration
First off, you need to know what’s going on. That means having good logs. If an attacker gets in, and you don’t have logs, it’s like trying to figure out a crime scene with no evidence. Attackers can even delete logs to cover their tracks, which is why sending them to a separate system, like a Security Information and Event Management (SIEM) platform, is a really smart move. This way, even if they mess with the firewall’s local logs, you’ve still got a record. Most experts suggest keeping logs for at least 14 days, but honestly, longer is usually better. It gives you a much clearer picture of any suspicious activity and helps in figuring out how an intrusion happened in the first place. Having this kind of visibility is key to spotting unusual patterns before they turn into a full-blown disaster. It’s about having that audit trail ready to go.
Prioritizing Vulnerability Management Beyond CVSS Scores
We all know about CVSS scores, right? They give you a number for how bad a vulnerability is. But relying solely on those numbers is a bit like driving by looking only at your speedometer. You know how fast you’re going, but not what’s happening on the road ahead. Attackers aren’t always going for the highest CVSS score; they’re going for what works. So, you need to look at which vulnerabilities are actually being exploited in the wild. If a lower-scoring vulnerability is being actively used to break into systems, that should be your priority. It means keeping up with threat intelligence reports and understanding the real-world tactics being used against devices like firewalls and SD-WANs. This is where understanding the attack vectors leading to a firewall hack becomes really important for prioritizing your patching efforts.
Implementing Comprehensive Security Hardening
This is where you really lock things down. It’s not just about patching; it’s about making the device itself as secure as possible. Think of it like reinforcing your house doors and windows even after you’ve fixed a broken lock. This involves several things:
- Disable unnecessary services: If a feature isn’t being used, turn it off. Less surface area means fewer ways for attackers to get in. For example, if you’re not using a specific SSO feature, disable it. This was a big deal with some recent FortiGate issues where disabling FortiCloud SSO helped block attacks.
- Strong authentication: Use multi-factor authentication (MFA) everywhere you can, especially for administrative access. Don’t rely on just passwords.
- Regularly review configurations: Make sure your firewall rules and settings are still appropriate and haven’t been accidentally weakened or tampered with. Check for any rogue accounts that might have been created.
- Network segmentation: Even if an attacker gets past the firewall, segmenting your network can limit how far they can move. This is a big help in stopping ransomware from spreading.
Doing these things might seem like a lot of work, but when you consider the alternative – a compromised network and potentially massive data loss – it’s definitely worth the effort. It’s about building a defense-in-depth strategy that doesn’t leave any single point of failure.
What’s Next?
So, we’ve seen how these firewalls, which are supposed to keep us safe, can actually become the weak link. Attackers are getting pretty good at finding ways in, whether it’s through new flaws or just using weak passwords. It’s a constant game of cat and mouse. The big takeaway here is that just having a firewall isn’t enough. We really need to pay attention to keeping them updated, logging what’s happening, and not forgetting about the basics. Because if the bad guys can get past our digital front door, everything else is at risk.
Frequently Asked Questions
Why are hackers interested in firewalls?
Firewalls are like the main gatekeepers of a computer network. Hackers want to get through them because once they do, they can access a lot of important information and move around the network easily. It’s like finding a secret way into a castle.
Are Fortinet firewalls being targeted a lot?
Yes, Fortinet FortiGate devices have been targeted. Attackers are using weak spots in these devices to get in and steal information, sometimes even creating fake accounts to get better access. They’ve gone after places like hospitals and government offices.
What about Cisco firewalls and SD-WANs?
Cisco firewalls and their SD-WAN systems have also seen a lot of attacks. Some of these attacks have been happening for a long time without anyone knowing, which is called a ‘zero-day’ exploit. Hackers use these weak spots to take control and even use ransomware.
How do hackers actually break into firewalls?
Hackers find different ways. Sometimes they exploit weaknesses in the parts of the firewall that manage it, even before a user logs in. Other times, they use automated tools to quickly create new accounts or trick systems that handle logins, like Single Sign-On.
What happens if a hacker gets into my firewall?
If a hacker hacks into a firewall, they can see everything happening on the network. They can then move to other computers, steal sensitive data, and even hold that data hostage until a ransom is paid. It’s a really bad situation for any organization.
How can I stop my firewall from getting hacked?
Keeping your firewall safe means keeping its software updated and checking for weak spots regularly. It’s also important to keep good records (logs) of what’s happening on the firewall and send them to a special security system. Making sure your firewall is set up securely and not using default passwords is also key.