Right then, let’s talk about staying safe online. It’s not as complicated as it sounds, honestly. We’re going to look at some basic security concepts, and I’ve put together a handy PDF guide for you. Think of it as a way to get your head around the digital world without all the confusing tech talk. We’ll cover threats, how to keep your accounts and devices secure, and just general good habits for when you’re browsing. It’s all about making things a bit clearer, so you can feel more confident online. This basic security concepts pdf should make things much easier to grasp.
Key Takeaways
- Watch out for dodgy emails and links that could be malware or scams.
- Make your passwords tough to guess and use two-factor authentication where you can.
- Keep your computer and phone software up to date to fix security holes.
- Be careful what you click on when you’re online and only download from trusted places.
- Think about what information you share and consider using encryption for private stuff.
Understanding Digital Threats
Right then, let’s talk about the digital nasties out there. It feels like every other day there’s a new way someone’s trying to get at your stuff online. It’s not just about dodgy emails anymore; the landscape has really changed.
Recognising Malware and Viruses
Malware, short for malicious software, is a big umbrella term for anything designed to mess with your computer or steal your information. Think of viruses, worms, trojans, and spyware. Viruses are the classic ones; they attach themselves to legitimate programs and spread when you run them. Worms are a bit more independent, able to replicate and spread across networks without needing to attach to anything. Trojans disguise themselves as useful software, but once you install them, they open a backdoor for attackers. Spyware, well, it spies on you, logging your keystrokes or tracking your browsing habits. Keeping your software updated is one of the simplest ways to block many of these threats. It’s like patching up holes in your digital fence before the foxes get in.
Identifying Phishing Scams
Phishing is all about trickery. Scammers pretend to be legitimate organisations – like your bank, a popular online store, or even a government agency – and send you emails or messages asking for personal details. They might say there’s a problem with your account, or that you’ve won a prize, and you need to click a link or download an attachment to sort it out. The link often leads to a fake website that looks real, where they can steal your login details or financial information. Always look closely at the sender’s email address; often, it’s slightly misspelled or uses a different domain. If something feels off, don’t click. It’s better to be safe than sorry, and you can always contact the organisation directly through their official website or phone number if you’re unsure. This kind of social engineering is surprisingly effective, and machine learning is increasingly used to spot these sophisticated attacks.
Understanding Ransomware Attacks
Ransomware is a particularly nasty type of malware. Once it infects your system, it encrypts your files, making them completely inaccessible. Then, the attackers demand a ransom payment, usually in cryptocurrency, to give you the decryption key. It can be devastating, especially for businesses, as it can halt operations entirely. Imagine all your important documents, photos, or work files suddenly locked away. The advice here is pretty straightforward: back up your data regularly and store those backups offline or on a separate system. That way, even if your main computer gets hit, you haven’t lost everything. It’s a tough situation, and cybersecurity studies show just how widespread this problem has become.
The digital world offers amazing convenience, but it also presents new challenges. Being aware of the common threats is the first step towards protecting yourself and your information. It’s not about being paranoid, but about being prepared.
Here’s a quick rundown of what to watch out for:
- Suspicious Links: Hover over links before clicking to see the actual URL. If it looks odd, don’t click.
- Urgency Tactics: Scammers often try to rush you into making a decision.
- Requests for Personal Info: Legitimate companies rarely ask for sensitive data via email.
- Unusual Attachments: Be wary of unexpected files, especially .exe or .zip files from unknown senders.
Staying informed about these threats is an ongoing process, but by understanding the basics, you’re already a good way ahead.
Securing Your Online Accounts
Think about all the places you log in online – email, social media, banking, shopping sites. Each one is a potential entry point for someone who shouldn’t be there. Keeping these accounts locked down is a big part of staying safe online. It’s not just about stopping hackers; it’s about protecting your personal information from falling into the wrong hands.
Creating Strong Passwords
This is the first line of defence, and honestly, it’s surprising how many people still use simple, easy-to-guess passwords. We’re talking about things like ‘password123’ or your pet’s name. Hackers have tools that can try millions of combinations very quickly, so a weak password is like leaving your front door wide open.
Here’s what makes a password strong:
- Length: Aim for at least 12 characters, but longer is always better.
- Variety: Mix uppercase and lowercase letters, numbers, and symbols (like !, @, #, $).
- Uniqueness: Don’t reuse the same password across multiple sites. If one account gets compromised, they all could.
- Randomness: Avoid using personal information like birthdays, addresses, or common words. Think random combinations.
Using a password manager can really help here. These tools generate and store strong, unique passwords for all your accounts, so you only need to remember one master password. It’s a game-changer for managing your digital life securely. You can find more guidance on managing your digital presence effectively here.
Implementing Two-Factor Authentication
Even with a strong password, there’s an extra layer of security you should absolutely be using: two-factor authentication (2FA). This means that even if someone gets your password, they still can’t log in without a second piece of proof. This usually comes in the form of a code sent to your phone, an authenticator app, or a physical security key.
Think of it like needing both a key and a secret handshake to get into a building. It makes it much harder for unauthorised people to gain access. Most major services like Google, Facebook, and your bank offer 2FA options. Make sure to turn it on wherever it’s available.
Managing Account Permissions
When you sign up for a new app or service, it often asks for permission to access certain parts of your other accounts. For example, a photo editing app might ask for access to your cloud storage, or a game might want to link to your social media profile. It’s easy to just click ‘allow’ without thinking.
However, it’s wise to review these permissions regularly. Do you really want that game to have access to your contacts? Does that app you used once six months ago still need access to your calendar? Limiting these permissions reduces the potential attack surface. For social media, you can often set your profile to private or friends-only and limit who can tag or mention you. Enabling login alerts for new devices or locations is also a good idea to monitor account activity on social media.
It’s easy to get lazy with online security, especially when things seem to be working fine. But a little bit of proactive effort now can save you a massive headache later. Regularly checking your accounts and updating your security settings isn’t a chore; it’s just part of being a responsible digital citizen in today’s world.
Protecting Your Devices
Keeping your digital life safe isn’t just about passwords and dodgy emails; it’s also about the actual gadgets you use every day. Think of your phone, laptop, or tablet as a little vault for your personal information. If that vault isn’t properly secured, well, you can see where this is going.
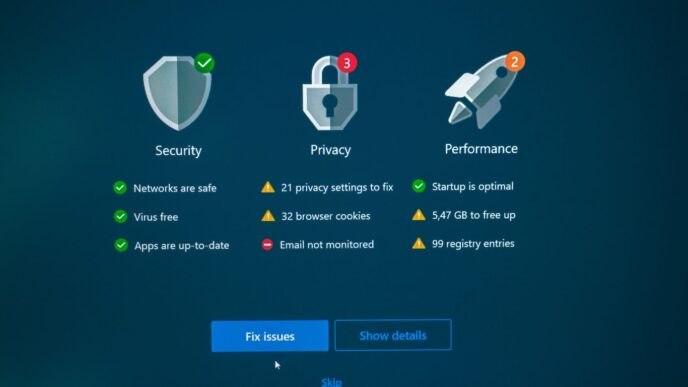
Keeping Software Updated
This is one of those things that’s easy to ignore, but it’s really important. Software updates, whether it’s for your operating system, your apps, or even your web browser, often contain fixes for security holes that have been discovered. Hackers are always looking for these weak spots, so patching them up as soon as possible is a smart move. It’s like fixing a leaky roof before the next big storm hits.
- Automatic Updates: Many devices and applications now offer automatic updates. Turn these on whenever possible. It means you don’t have to remember to do it yourself.
- Manual Checks: For anything that doesn’t update automatically, make it a habit to check for updates at least once a month. Your device will usually prompt you, but it’s good to be proactive.
- App Stores: When you get an update notification from your phone’s app store, don’t put it off. These updates can be just as vital as system-wide ones.
Using Antivirus Software
Even with updates, sometimes nasty bits of software, like malware or viruses, can still find their way onto your devices. Antivirus software acts as a guard, scanning files and programs for anything suspicious. It can often detect and remove threats before they cause any real damage. For many people, having a good antivirus program is a non-negotiable part of device security. It’s worth looking into reputable options, as some free versions might not offer the same level of protection as paid ones. A good antivirus can be your first line of defence against a whole host of digital nasties.
Securing Your Home Wi-Fi Network
Your home Wi-Fi is like the front door to your digital life when you’re at home. If someone can easily get onto your network, they can potentially see what you’re doing online or even access devices connected to it.
Here are a few steps to make sure your Wi-Fi is locked down:
- Change the Default Router Password: Routers come with a default username and password that are often publicly known. Change these immediately to something unique and strong.
- Use WPA3 Encryption: If your router supports it, use the latest security protocol, WPA3. If not, WPA2 is the next best thing. Avoid older, weaker encryption methods like WEP.
- Create a Strong Wi-Fi Password: This is the password you use to connect devices to your network. Make it long, complex, and not easily guessable.
- Consider a Guest Network: Most modern routers allow you to set up a separate network for visitors. This keeps your main network, and the devices on it, separate and more secure.
Keeping your devices updated and protected isn’t a one-off task. It requires ongoing attention, much like maintaining your home. Regularly checking for software patches and ensuring your network is secure are simple yet effective ways to keep your personal information out of the wrong hands. For Apple users, features like Face ID and Touch ID offer an extra layer of hardware-based security that’s hard to bypass.
Remember, securing your devices is a key part of overall online safety. It’s about making sure that the personal information you store and transmit is as safe as possible. Setting up unique passcodes for your devices, for instance, is a basic but vital step in preventing unauthorised access.
Safe Browsing Habits

When you’re online, it’s easy to get caught up in what you’re doing and forget that there are risks. Just like you wouldn’t walk down a dark alley without looking, you shouldn’t browse the internet without some common sense. It’s about being aware of your surroundings, digitally speaking.
Recognising Secure Websites
One of the first things to look out for is how a website presents itself. You’ll often see a little padlock icon next to the web address in your browser’s bar. This padlock means the connection between your browser and the website is encrypted, which is good. It’s a sign that the site is trying to protect your information. Also, check the web address itself. Does it look right? Sometimes scammers will use addresses that are very similar to legitimate ones, but with a slight change. For example, instead of ‘amazon.co.uk’, it might be ‘amazzon.co.uk’. Always double-check these details, especially if you’re about to enter any personal information or make a purchase. For parents wanting to help their children stay safe, understanding these basics is a good start to making them "Web aware" [8e38].
Avoiding Suspicious Downloads
Downloading files from the internet can be handy, but it’s also a common way for malware to sneak onto your computer. Think before you click that download button, especially if it’s from a source you don’t recognise or if the file seems too good to be true. Free software, music, or movies offered from unofficial sites are often bundled with nasty surprises. If you’re unsure about a download, it’s best to leave it. Sometimes, even legitimate-looking emails can contain links to malicious downloads, so be cautious with attachments and links in emails too.
Managing Browser Cookies and Cache
Your web browser keeps a record of your online activity, like a digital diary. This includes cookies, which websites use to remember you and your preferences, and cache, which stores parts of websites to help them load faster. While these aren’t inherently bad, they can sometimes pose privacy risks. Over time, they can build up and might reveal information about your browsing habits. Regularly clearing your cookies and cache can help reduce this. Most browsers have settings that allow you to do this easily. It’s a simple step that can make a difference in keeping your online footprint a bit smaller.
Being mindful of where you click and what you download is a big part of staying safe online. It’s not about being scared, but about being smart and aware of the potential pitfalls.
Data Privacy Essentials
So, we’ve talked about keeping your accounts safe and your devices locked down, but what about your personal information? It’s a big deal these days, and frankly, it’s easy to lose track of where it all goes. Understanding what data is collected and how it’s used is the first step to protecting it.
Understanding Personal Data
Personal data is basically any information that can identify you. Think about your name, address, email, phone number, but also things like your online browsing history, your location data, and even your opinions if they’re linked to you. It’s not just the obvious stuff. Companies collect a lot of this, sometimes without us even realising it. It’s worth looking into the ESSENTIALS OF DATA GOVERNANCE, PRIVACY, AND PROTECTION to get a clearer picture.
Controlling Information Sharing
This is where you get to take some control. Most apps and websites have privacy settings. It might take a bit of digging, but you can often limit what information is shared. For example, you can turn off location services for apps that don’t really need it. You can also be mindful of what you post on social media. Think before you share. Here are a few things to consider:
- Review app permissions regularly.
- Adjust privacy settings on social media platforms.
- Be cautious about filling out online forms.
- Opt out of data sharing where possible.
The Importance of Encryption
Encryption is like a secret code for your data. When data is encrypted, it’s scrambled so that only authorised people can read it. This is super important for sensitive information, like your bank details or private messages. It means that even if someone managed to get hold of your data, they wouldn’t be able to understand it without the key. Following good Cybersecurity and Data Security guidelines often means using encryption where appropriate.
It’s easy to feel overwhelmed by all this, but small, consistent actions make a big difference. Don’t just accept default settings; take a moment to see what’s going on with your information.
Physical Security Measures

We’ve talked a lot about online stuff, but what about the real world? Sometimes, the biggest risks aren’t digital at all. It’s about making sure nobody can just walk up and grab your laptop or peek at your screen. Think of it as locking your front door – you wouldn’t leave it wide open, right? The same logic applies to your tech.
Securing Your Workstation
This is pretty straightforward. When you’re at your desk, especially in a shared space, keep your screen locked when you step away. A quick Windows key + L (or Ctrl + Cmd + Q on a Mac) does the trick. It stops prying eyes from seeing what you’re working on, or worse, logging into your accounts. Also, be mindful of where you position your screen. If you’re in a public place, like a coffee shop, angle it away from windows or busy walkways. It’s about creating a bit of a privacy bubble around your work.
Protecting Sensitive Documents
Not everything is digital, of course. Paper documents can hold just as much sensitive information. If you’re printing anything confidential, make sure you collect it straight away. Don’t leave printouts sitting in the office printer tray. When you’re done with them, shred them properly. A cross-cut shredder is much better than just tearing things up. For really important stuff, consider a secure filing cabinet with a lock. It might seem old-fashioned, but it works.
Device Disposal Best Practices
So, you’ve got an old laptop or phone you’re getting rid of. Just deleting files isn’t enough. People can often recover deleted data with the right tools. For hard drives, the best bet is physical destruction – drilling holes through them or using a professional service. If you’re donating or selling, make sure you do a full factory reset and then overwrite the storage with junk data. This makes it much harder for anyone to get your old information. It’s a key part of physical security measures to prevent data leaks.
It’s easy to get caught up in the digital side of security, but the physical world matters just as much. Think about who can see your screen, who can access your devices when you’re not there, and what happens to your old tech. These steps might seem small, but they add up to a much safer setup overall.
Here’s a quick rundown of what to do:
- Lock your screen when you leave your desk.
- Shred sensitive paper documents.
- Wipe or destroy old storage media before disposal.
- Be aware of your surroundings when working in public.
Remember, security is layered. You need to think about both the digital and the physical aspects to keep your information safe. Even temporary setups, like for events, need careful consideration of these physical aspects for a set duration.
Wrapping Up
So, that’s a look at some basic security ideas. It might seem like a lot at first, but really, it’s about taking small steps to keep yourself and your stuff safer online. Think of it like locking your front door – you wouldn’t leave it wide open, right? The same applies to your digital life. Keep these points in mind, and you’ll be in a much better spot. Don’t get overwhelmed; just start with one or two things and build from there. Staying aware is half the battle, and hopefully, this guide has given you a good starting point.
Frequently Asked Questions
What’s the difference between a virus and malware?
Think of malware as a big umbrella word for any nasty software designed to harm your computer. A virus is just one type of malware, like a specific kind of germ. Other types include spyware that spies on you or ransomware that locks your files and demands money.
How can I spot a fake email (phishing)?
Phishing emails often try to rush you. They might have spelling mistakes, ask for personal details like passwords or bank info, or have links that look a bit ‘off’. Always double-check the sender’s address and be suspicious of urgent requests.
Why is it important to create strong passwords?
A strong password is like a sturdy lock on your digital door. If it’s weak, like ‘12345’ or your pet’s name, it’s super easy for hackers to guess and get into your accounts, stealing your information.
What is two-factor authentication (2FA) and why use it?
2FA adds an extra layer of security. It’s like needing two keys to open a door. Besides your password, you’ll need a second code, usually sent to your phone, to log in. This makes it much harder for someone to break into your account even if they steal your password.
Why should I keep my software updated?
Software updates aren’t just about new features. They often fix security holes that hackers could use to get into your devices. Keeping things updated is like patching up cracks in your defences.
What does ‘encryption’ mean for my data?
Encryption scrambles your data so that only someone with the right ‘key’ can read it. It’s like writing a secret message in a code. This protects your sensitive information, like passwords or private messages, from being understood if it falls into the wrong hands.