It feels like every other week there’s a new headline about a cyber attack. Keeping your computer safe from viruses and other nasty online stuff is getting more complicated, that’s for sure. Things are changing fast, and what worked last year might not be enough today. We’re going to look at what’s new in the world of computer viruses latest threats and how you can stay protected. It’s not just about big companies; everyone needs to be aware.
Key Takeaways
- Fileless malware and AI-driven attacks are becoming more common, making them harder for older security tools to catch.
- Viruses still spread through emails, sketchy websites, and bad downloads, so be careful what you click or install.
- Ransomware and cryptojacking are serious threats that can cost you a lot of money or slow down your computer.
- Working from home opens up new ways for attackers to get in, so secure your home network and devices.
- Staying updated, using good antivirus software, and strong passwords with multi-factor authentication are your best defenses.
Understanding Evolving Computer Viruses Latest Threats

Things are getting pretty wild out there in the digital world, and the bad guys are constantly cooking up new ways to mess with our computers. It’s not just about those old-school viruses that attach to files anymore. We’re seeing some really sneaky stuff that makes you wonder how they even get in.
The Rise of Fileless Malware
One of the biggest headaches right now is fileless malware. Think of it like a ghost – it doesn’t leave a physical file behind for your antivirus to easily spot. Instead, it sneaks into your computer’s memory or uses legitimate tools already on your system, like PowerShell or the Windows Registry, to do its dirty work. This makes it super hard for older security programs to even know it’s there. It’s like trying to catch smoke. This shift means we have to rely more on security software that watches what programs do, not just what files they are.
AI-Powered Cyber-Attacks
Artificial intelligence isn’t just for making cool art or helping you write emails anymore. Attackers are using AI too, and it’s making their efforts much more effective. They can use AI to quickly find weaknesses in systems, craft incredibly convincing phishing messages that are tough to spot, and even change their malicious code on the fly to avoid detection. This is why just having a basic antivirus isn’t always enough; you need something smarter that can adapt. The cyber threat landscape is changing fast because of this.
Deepfake Technology’s Growing Influence
Deepfakes are getting scarily good. You might have seen funny face-swap videos, but the technology is also being used for much more serious and harmful purposes. Imagine getting a video call from your boss asking for urgent financial transfers, but it’s actually a deepfake. Or seeing a fake news report that looks completely real. This technology plays on our trust and can be used to spread misinformation or trick people into giving up sensitive information. It’s a whole new level of social engineering that we need to be aware of.
How Computer Viruses Spread in 2026
Even with all the fancy new tech out there, the ways viruses get onto our computers haven’t changed that much. It’s still mostly about tricking us into letting them in, or finding tiny cracks in our digital defenses. Think of it like this: most of the time, we’re the ones opening the door, even if we don’t realize it.
Infected Email Attachments and Links
Email is still a huge culprit. Attackers send messages that look totally normal – maybe a fake invoice, a password reset notification, or a shared document. But inside that attachment or link is the nasty stuff. Clicking that link might take you to a fake login page designed to steal your passwords, or the attachment itself could be a program that installs malware the second you open it. It’s a classic trick, but it works because we’re all so used to checking emails for work and personal stuff.
Malicious Websites and Fake Downloads
This one’s a bit like the email scam, but it happens when you’re browsing. You might land on a website that looks legit, but it’s actually trying to trick you. It could be a pop-up saying your computer is infected and you need to download a
Advanced Malware and Their Tactics
Things have gotten pretty wild out there in the digital world. It’s not just about simple viruses anymore; we’re talking about malware that’s really learned some new tricks. These aren’t your grandpa’s computer bugs. They’re designed to be sneaky and stick around, making them a real headache to deal with.
Sophisticated Ransomware Campaigns
Ransomware is still a huge problem, and it’s gotten way more aggressive. Attackers aren’t just locking up your files; they’re often stealing them first and then threatening to leak them if you don’t pay. This double-whammy approach, sometimes called double extortion, puts a lot of pressure on businesses. The demands can be massive, too. We’re seeing millions of dollars being paid out, and it’s hitting industries like manufacturing and healthcare hard. It’s a tough situation because paying doesn’t even guarantee you’ll get your data back or that they won’t come back for more.
Worms Evading Network Detection
Remember worms? They’re back, and they’re smarter. These things can spread on their own across networks, and the latest versions are really good at hiding. They can mimic normal network traffic, making it super hard for security systems to spot them. This means a worm could be quietly spreading through your company’s network without anyone noticing until it’s too late. It’s a big reason why just having basic antivirus isn’t enough anymore; you need systems that can spot unusual behavior like AI-driven threats.
Cryptojacking’s Stealthy Resource Hijacking
Cryptojacking is kind of like a silent thief. Instead of stealing your files or demanding money, these attackers secretly use your computer’s power to mine cryptocurrency. You might not even notice it at first, but your computer will start running slower, your electricity bill might go up, and components could wear out faster. It’s a low-profile attack, but it drains resources and can cause real damage over time. It’s a good example of how threats are evolving to be less obvious but still harmful.
The Impact of Remote Work on Security

The big shift to working from home, which really took off a few years back, has totally changed how businesses need to think about security. It’s not just about locking down the office anymore. Suddenly, everyone’s computer is a potential entry point, and that’s a huge deal.
Widened Attack Surfaces for Remote Employees
Think about it: when everyone’s in the office, IT has a pretty good handle on the network. Devices are usually company-issued, and the Wi-Fi is controlled. But when people work from home, that all goes out the window. They might be using their personal laptops, connecting to public Wi-Fi at a coffee shop, or just have a less secure home network. This creates a much bigger target for bad actors. By 2025, a significant 92% of IT professionals anticipated that remote work would escalate cybersecurity threats. This means the usual defenses just aren’t enough anymore. We’re seeing more attempts to trick remote workers into clicking malicious links or opening infected files, which is why understanding phishing variants is so important.
Endpoint Compromise Risks
An endpoint is basically any device that connects to your network – laptops, phones, tablets. When these devices are outside the controlled office environment, they’re more vulnerable. If a remote worker’s personal device gets infected with malware, that malware can then potentially spread to the company network. This is especially risky if they’re using the same device for both work and personal stuff. It’s a constant battle to keep all these different devices patched and secure.
Data Exfiltration from Home Networks
Another big worry is data getting out. When employees are working from less secure home networks, it’s easier for attackers to intercept data or even gain access to sensitive files. Imagine someone’s home Wi-Fi being compromised; suddenly, all the company data they’re accessing could be exposed. This is why strong encryption and secure connections, like VPNs, are absolutely vital for anyone working remotely. It’s not just about preventing attacks; it’s also about making sure the data stays where it belongs.
Key Strategies for Computer Virus Prevention
So, how do we actually stop these digital nasties from messing with our stuff? It’s not about one magic bullet, but more like building a strong fence with a few different locks. Think of it as a layered approach to keeping your computer safe. The goal is to make it as hard as possible for viruses to get in and cause trouble.
Maintaining Up-to-Date Software and Systems
This is probably the most basic, yet often overlooked, step. Software developers are constantly finding and fixing security holes in their programs. When you delay updates, you’re basically leaving those doors unlocked for attackers. It’s like knowing there’s a weak spot in your fence but deciding not to fix it. Automated bots are always scanning for these unpatched gaps, so keeping your operating system and applications current is a big deal. It patches those known security holes before bad actors can exploit them. Don’t wait weeks or months; install updates when they become available.
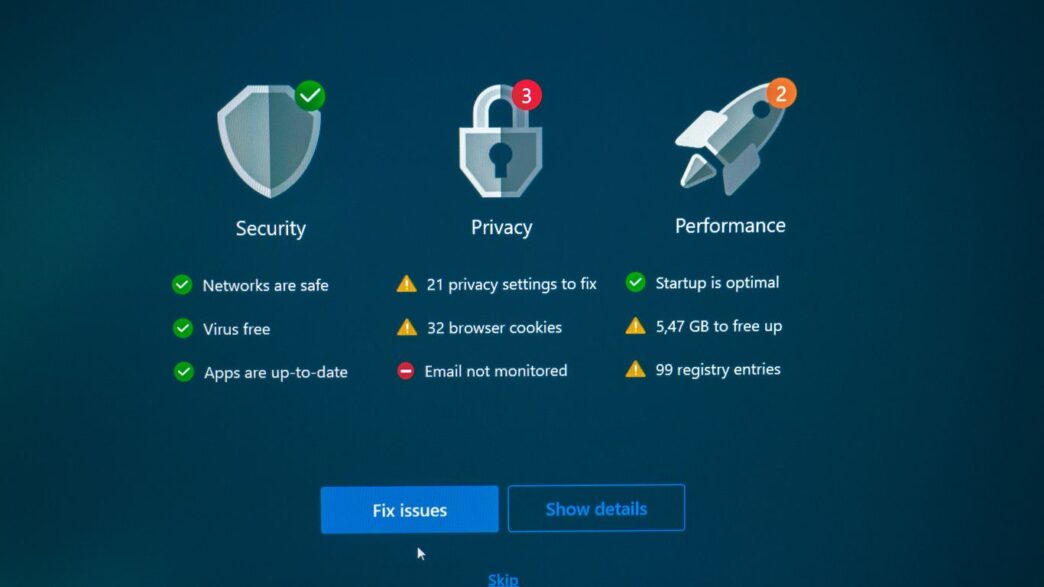
Utilizing Trusted Antivirus and Real-Time Protection
Having a good antivirus program is like having a security guard for your computer. But it’s not enough to just have one installed; it needs to be active and scanning all the time. We’re talking about real-time protection that watches for suspicious activity, not just when you tell it to scan. The best tools use behavior-based detection, meaning they can spot unusual actions even if they don’t recognize the specific virus. This helps block potentially unwanted apps and stops risky scripts before they can spread deeper into your system. It’s a proactive measure that catches threats in the act.
Implementing Strong Passwords and Multi-Factor Authentication
Passwords alone just aren’t cutting it anymore. Attackers are getting really good at stealing credentials through phishing scams or special malware. That’s where multi-factor authentication (MFA) comes in. It adds an extra layer of security, usually a code sent to your phone or an app. Even if someone gets your password, they still can’t get into your account without that second factor. This significantly limits the damage if an account does get compromised. Think of it as needing two keys to open a very important door. For a deeper dive into password security, check out tips on password management.
Here’s a quick look at what makes a strong password and why MFA is so important:
- Password Strength:
- Use a mix of uppercase and lowercase letters.
- Include numbers and symbols.
- Avoid common words or personal information.
- Make it long – longer is generally better.
- MFA Benefits:
- Adds a critical security layer.
- Protects against stolen or weak passwords.
- Reduces the risk of account takeover.
- Provides peace of mind for sensitive accounts.
Combating Social Engineering Tactics
Social engineering is a tricky business. It’s not about breaking into systems with fancy code; it’s about tricking people into doing the hacker’s bidding. Think of it as psychological manipulation for digital gain. These attacks prey on our natural tendencies to trust, to be helpful, or to react quickly when something seems urgent. And honestly, they’re getting more sophisticated every year.
Recognizing Email Phishing Variants
Phishing emails are still a huge problem. They look like they’re from your bank, your favorite online store, or even your boss. They might say there’s a problem with your account, or that you’ve won a prize, or that you need to review an important document. The goal is usually to get you to click a link or open an attachment. Clicking that link could lead to a fake login page designed to steal your passwords, or it could download malware onto your computer. It’s a classic trick, but it still works because the emails can look incredibly convincing. Sometimes they even use information about you that they’ve found online to make it seem more real. It’s a good idea to be suspicious of any unexpected email asking for personal details or urging immediate action. Remember, legitimate companies rarely ask for sensitive information via email. You can often verify by going directly to the company’s website yourself, rather than clicking a link in the email. This is a common way attackers try to get your login details for various services.
Identifying Spear Phishing and Whaling Attempts
Spear phishing takes things up a notch. Instead of sending a generic email to thousands of people, attackers do their homework. They’ll research you or your company and craft a message that seems like it’s coming from someone you know – maybe a colleague, a vendor, or even your IT department. They might pretend to have an urgent issue that needs your immediate attention, like a problem with a recent software update or a request for payment details. Whaling is similar, but it targets the big fish – executives, CEOs, or other high-level employees. The idea is that if they can trick a senior person, they might gain access to more sensitive information or authorize larger financial transfers. These attacks are harder to spot because they’re so personalized. Always double-check requests that seem unusual, even if they appear to come from someone you know. A quick phone call or a separate message can often prevent a disaster. Attackers are also using voice phishing, or vishing, more often now, so be wary of unexpected calls asking for sensitive data.
Understanding the Psychology Behind Exploits
At its core, social engineering is about understanding human behavior. Attackers exploit our desire to be helpful, our fear of missing out, or our tendency to follow instructions. They create a sense of urgency, making us feel like we need to act fast without thinking. They might also play on our curiosity, offering something tempting like a free download or a sneak peek at something exclusive. Sometimes, they just impersonate authority figures to get us to comply. It’s a bit like a magician distracting you while they perform their trick. The best defense is to be aware of these tactics and to pause before reacting. Ask yourself: Is this request legitimate? Is there a reason I’m being rushed? Who is this person really? By taking a moment to think critically, you can often see through the deception. Learning about these evolving methods, like the rise of "ClickFix" attacks, is key to staying safe online. It’s a constant game of cat and mouse, and staying informed is your best weapon.
Proactive Defense Against Emerging Threats
Okay, so we’ve talked a lot about the bad stuff – the viruses, the hacks, the whole digital nightmare. But what can we actually do about it before things get really messy? It’s all about getting ahead of the game, you know? Instead of just reacting when something goes wrong, we need to build defenses that are smart and ready for whatever’s next. This means looking beyond just the basic antivirus software and thinking about the bigger picture.
The Urgency of Vulnerability Management
Think of your computer systems like a house. You wouldn’t leave a window unlocked, right? Well, vulnerabilities are like those unlocked windows. They’re weak spots that attackers can sneak through. Keeping software updated is a big part of this, but it’s more than just hitting ‘update now.’ It’s about actively looking for and fixing these weak spots before anyone else finds them. Companies that really focus on this are way less likely to end up in the news for a data breach. It’s about having a good inventory of everything you have and knowing where the potential problems are. This is a big part of Continuous Threat Exposure Management.
Adopting Behavior-Based Detection Systems
Traditional security often looks for known bad guys – like a bouncer checking IDs against a list. But what about the new threats that don’t have a known ID yet? That’s where behavior-based detection comes in. These systems watch how things act on your network. If your computer suddenly starts acting super weird, like trying to send out tons of data it normally wouldn’t, this system flags it. It’s like having a security guard who notices someone acting suspiciously, even if they aren’t on a watchlist. This is especially important with the rise of AI-powered attacks, which can be pretty unpredictable. These systems can spot unusual patterns that might signal something like malicious open-source components being used.
Regularly Backing Up Critical Data
This one might sound simple, but honestly, it’s probably the most important safety net. If the worst happens – ransomware locks everything up, or a system just crashes – having a solid backup means you can get back to normal without losing everything. It’s not just about having backups, though. You need to make sure they’re stored safely, maybe even offline, so the attackers can’t get to them too. Think about it: if your main files are gone, but you have a clean copy from last week, you’ve basically dodged a massive bullet. It’s about resilience, being able to bounce back even when things get tough.
Staying Ahead of the Game
So, we’ve talked about a lot of scary stuff, right? From sneaky fileless malware that hides in your computer’s memory to AI that’s getting scarily good at tricking us, the digital world keeps throwing new curveballs. It’s easy to feel overwhelmed, but the good news is, we’re not helpless. Keeping your software updated, being super careful about what you click on, and using strong passwords with that extra layer of security like multi-factor authentication are still your best bets. Think of it like locking your doors and windows – basic, but it works. And hey, backing up your important files regularly? That’s your safety net if the worst happens. The landscape is always changing, but by staying aware and taking these simple steps, you can make yourself a much tougher target for those looking to cause trouble online.
Frequently Asked Questions
What’s new with computer viruses in 2026?
In 2026, viruses are getting smarter. Instead of just being files, some can hide in your computer’s memory without leaving a trace. Others use Artificial Intelligence (AI) to create trickier fake messages or find weaknesses faster. Even fake videos and audio, called deepfakes, are being used to fool people.
How do viruses get onto computers these days?
Viruses still sneak in through emails with fake attachments or links, and through websites that look real but are actually dangerous. Downloading software from untrustworthy places or using unsafe browser add-ons are also common ways for viruses to get in. Even old methods like using infected USB drives can still work.
What’s so bad about ransomware?
Ransomware is like a digital kidnapper. It locks up your important files by scrambling them, and then demands money to unlock them. This can stop businesses and people from accessing their data, causing huge problems and costs.
How does working from home make computers more at risk?
When people work from home, they often use home internet and personal devices, which might not be as secure as office networks. This creates more ways for hackers to get in, steal information, or cause trouble, especially if they can trick remote workers.
What’s the best way to avoid getting a virus?
Keeping your computer’s software updated is super important because updates fix security holes. Using good antivirus software that checks for threats all the time helps a lot. Also, using strong, unique passwords and turning on extra security steps like multi-factor authentication makes it much harder for hackers.
What are social engineering attacks?
These attacks play on people’s feelings and trust. Hackers pretend to be someone they’re not, like a friend, a boss, or a tech support person, to trick you into giving them information or clicking on something bad. They might send fake emails (phishing) or target specific people with very convincing messages (spear phishing).