Keeping your systems safe from digital bad guys is a big job. It’s not just about finding the problems, but actually fixing them. This guide is here to walk you through how to get those vulnerability fixes done right, from setting up a good system to making sure the fixes stick. We’ll look at how to figure out what’s most important to fix first and how to actually get the work done, even when things get complicated. Let’s get those systems patched up.
Key Takeaways
- Build a solid plan for finding and fixing security holes. This means having clear rules, using the right tools, and getting support from the top brass.
- Figure out which security problems are the most urgent. Look at how much damage they could do to your business and how easy they are for attackers to use.
- When you find a security weakness, fix it completely if you can. If not, put temporary measures in place to lower the risk while you plan a permanent fix.
- Make the process of fixing security issues faster by using automation. Connect your systems so tasks get assigned quickly and rely less on people doing everything manually.
- Keep an eye on how well your fixes are working and report on your progress. Use this information to make your security efforts even better over time.
Establishing A Robust Vulnerability Management Program
Alright, let’s talk about getting a solid handle on security weaknesses. You can’t just react when something bad happens; you need a plan. That’s where a good vulnerability management program comes in. Think of it as your security’s foundation. Without it, you’re just hoping for the best, and that’s not a strategy.
Defining Clear Policies and Procedures
First things first, you need rules. What happens when a vulnerability is found? Who does what? When does it need to be fixed? Having clear, written-down policies makes sure everyone is on the same page. It stops confusion and makes sure things actually get done. You’ll want to map out the whole process:
- Discovery: How do you find these weaknesses? Regular scans? Bug bounty reports?
- Assessment: How bad is it? Does it need fixing today or next week?
- Remediation: Who fixes it? How do they fix it?
- Verification: How do you know it’s actually fixed?
These steps need clear timelines. For example, a critical vulnerability might need a fix within 24 hours, while a low-risk one could have a month. Documenting everything is key for accountability and for showing auditors you’re doing your job.
Leveraging Advanced Vulnerability Management Tools
Trying to track all your systems and their potential problems manually is a recipe for disaster. You need tools. These aren’t just fancy scanners; they help automate a lot of the grunt work. Think about software that can scan your network, find outdated software, or spot misconfigurations. Some tools can even help prioritize what to fix first based on how likely it is to be exploited. Using the right technology makes the whole process faster and less prone to human error. It’s about working smarter, not harder, to keep your digital doors locked.
Securing Leadership Support and Buy-In
This is a big one. You can have the best policies and the coolest tools, but if the people in charge don’t care, nothing will happen. You need your leaders to understand why this is important. It’s not just an IT problem; it’s a business problem. A security breach can cost a fortune in lost data, downtime, and damaged reputation. When leaders support vulnerability management, they’re more likely to approve budgets for tools, give teams the time they need to fix things, and make security a priority across the whole company. Getting that buy-in means explaining the risks in terms the business understands – like money and reputation.
Prioritizing Vulnerability Fixes Effectively
Okay, so you’ve found a bunch of vulnerabilities. Now what? You can’t just fix everything at once, right? It’s like having a huge to-do list; you gotta figure out what’s most important. This is where prioritizing comes in. It’s not just about the fancy technical score; it’s about what actually matters to your business.
Assessing Business Impact and Risk Factors
First off, think about what would happen if a hacker actually got in through this specific weakness. Would it shut down your main service? Would customer data get stolen? Would it cost a ton of money or ruin your company’s reputation? Some vulnerabilities might look bad on paper, but if exploiting them wouldn’t really hurt your business much, they can wait a bit. On the flip side, a vulnerability that could cripple your operations needs immediate attention, even if its technical severity score isn’t the absolute highest.
- Data Loss: How much sensitive information could be exposed?
- Service Disruption: Could this take down critical systems or websites?
- Financial Impact: What are the direct monetary costs of an exploit?
- Reputational Damage: How would this affect customer trust and public perception?
Evaluating Exploit Difficulty and Code Availability
Next, consider how easy it is for someone to actually use this vulnerability. Is there already a tool, like a script or program, floating around the internet that makes exploiting it simple? If exploit code is readily available, that vulnerability becomes a much bigger deal, even if it’s not the most complex one. It’s like leaving your front door unlocked versus having a complicated lock that requires special tools to pick. The unlocked door is a much bigger, immediate problem.
- Exploit Code Existence: Is there a ready-made tool to exploit this?
- Exploit Difficulty: How much skill or effort does it take to exploit?
- Remote Exploitation Potential: Can someone attack this from the internet, or does it require local access?
Considering Existing Security Controls
Don’t forget about the security measures you already have in place. Sometimes, even if a vulnerability exists, your existing defenses might make it really hard for an attacker to actually succeed. Maybe you have strong network segmentation, or advanced intrusion detection systems. These existing controls can lower the actual risk posed by a vulnerability. It’s not a reason to ignore it completely, but it might mean you can place it a little lower on the priority list compared to a vulnerability that has no other defenses protecting it. It’s about understanding the whole picture, not just the single weak spot.
Implementing Strategic Remediation Approaches
Once you’ve got a handle on what’s broken, the next big step is figuring out how to actually fix it. This isn’t just about slapping a band-aid on things; it’s about having a plan. We’re talking about different ways to deal with these security holes, depending on how bad they are and what resources you have.
Executing Full Remediation Through Patching and Updates
This is the gold standard, right? You find a vulnerability, and you completely fix it. Usually, this means applying a patch or an update that the software vendor released. It’s the most thorough way to go because it addresses the root cause of the problem. Think of it like fixing a leaky pipe instead of just putting a bucket under it. The goal here is to eliminate the vulnerability entirely. It’s best to test these patches in a safe environment first, though, so you don’t accidentally break something else. Nobody wants to fix one problem only to create two more.
Employing Mitigation Strategies for Temporary Risk Reduction
Sometimes, you can’t just patch something right away. Maybe the vendor hasn’t released a fix yet, or the fix is too complex to implement immediately without disrupting your business. That’s where mitigation comes in. It’s like putting up a temporary barrier to stop people from getting hurt while you plan a permanent fix. This could involve changing firewall rules, disabling a specific feature, or adding extra monitoring. It doesn’t get rid of the vulnerability, but it makes it a lot harder for someone to exploit it. It buys you time to do the real fix later.
Documenting Acceptance of Low-Risk Vulnerabilities
Not every single vulnerability needs a full-blown remediation effort. Some are just too minor, or the cost and effort to fix them would be way more than the potential damage they could cause. In these cases, you might decide to accept the risk. This isn’t a decision to take lightly, though. You need to have a solid reason, like having other security measures already in place that protect against that specific issue. It’s super important to document why you’re accepting the risk. This way, if something does happen down the line, you can show you made a conscious, informed decision. It’s all about managing risk intelligently, not just blindly fixing everything.
Automating And Streamlining Vulnerability Fixes
Let’s face it, manually tracking down and fixing every single security flaw is a huge pain. It takes forever, and honestly, it’s easy to miss things when you’re swamped. That’s where automation comes in. Automated vulnerability remediation streamlines the process of identifying, prioritizing, and fixing system weaknesses. This approach significantly reduces the need for manual intervention, leading to faster and more efficient security management.
Automating Remediation Workflows
Think about how much time you spend just looking for the next thing to fix. Tools can do a lot of that heavy lifting. You can set up systems to automatically scan for new issues, check if patches are available, and even push those patches out to your systems. This means less time spent on repetitive tasks and more time for the complex stuff. It’s all about making the whole process smoother and quicker.
Integrating With Ticketing Systems for Task Assignment
Once a vulnerability is found and needs fixing, who gets the job? Instead of emails getting lost or tasks falling through the cracks, you can connect your security tools directly to your team’s ticketing system. This way, when a vulnerability pops up, a ticket is automatically created and assigned to the right person or team. It keeps everyone in the loop and makes sure nothing gets forgotten. It’s a pretty neat way to keep track of who’s doing what and when it’s supposed to be done.
Reducing Dependency on Manual Processes
Manual work is slow and prone to mistakes. When you rely on people to manually check systems, apply patches, and report on progress, things can get delayed. Automation helps cut down on these manual steps. This means fewer errors, faster fixes, and a more consistent security posture. It’s a big step towards a more proactive security setup, moving away from just reacting to problems. You can find more on how to get started with automated vulnerability remediation if you’re looking to speed things up.
Continuous Monitoring And Progress Reporting
So, you’ve gone through the whole process of finding and fixing those pesky vulnerabilities. Great job! But honestly, that’s not the end of the story. Think of it like cleaning your house; you can’t just do it once and expect it to stay spotless forever. You’ve got to keep an eye on things. This is where continuous monitoring and reporting come into play. It’s all about making sure the fixes stick and that you’re not letting new problems sneak in.
Tracking Remediation Outcomes and Timelines
First off, you need to know if your fixes actually worked. Did that patch really close the security hole? Or did it cause some other weird issue? You’ve got to track what happened after you applied a fix. This means checking back in, maybe running another scan, and seeing if the vulnerability is truly gone. It’s also super important to keep tabs on how long this whole process takes. Are you fixing things quickly, or are they sitting around for ages? Knowing this helps you spot bottlenecks. Maybe your patching process is slow, or perhaps certain teams are taking too long to respond.
Here’s a quick look at what you might track:
- Vulnerability Age: How long has a vulnerability been open?
- Time to Remediate: How long from discovery to fix?
- Patching Success Rate: Did the patches work as expected?
- Number of Reopened Vulnerabilities: How often do fixes fail?
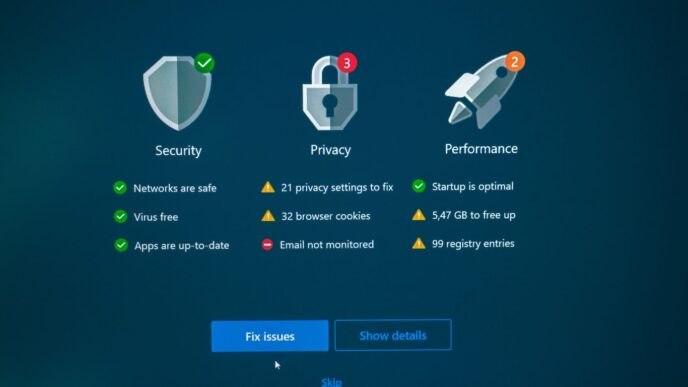
Utilizing Dashboards for Real-Time Risk Insights
Nobody wants to dig through spreadsheets to figure out what’s going on. That’s why dashboards are your best friend here. They give you a quick, visual snapshot of your security status. You can see at a glance which vulnerabilities are the most critical, where they are, and how your team is doing on fixing them. These visual tools are key for keeping everyone, from the tech folks to the higher-ups, in the loop. A good dashboard can show you trends, highlight urgent issues, and even compare your progress against set goals or service level agreements (SLAs). It makes it way easier to understand your overall risk level without getting lost in the details. Tools like Orca Security can help provide these kinds of insights.
Adapting Strategies Based on Performance Metrics
Looking at your progress reports and dashboards isn’t just for show. It’s about learning and getting better. The threat landscape is always changing, and so are your systems. What worked last month might not work today. You need to look at the data – are you seeing a lot of the same vulnerabilities popping up? Are new types of threats emerging? Based on this, you might need to tweak your approach. Maybe you need to invest in better tools, provide more training for your teams, or adjust your patching priorities. It’s a cycle: monitor, report, analyze, and then adjust. This way, you’re not just reacting; you’re actively improving your defenses over time.
Addressing Challenges in Vulnerability Management
Look, nobody said managing vulnerabilities would be a walk in the park. It’s often messy, and things don’t always go according to plan. We’ve talked about the ideal setup, but let’s get real about the bumps in the road.
Overcoming Poor Visibility in Complex Environments
This is a big one. So many companies have sprawling IT setups these days – cloud stuff, on-prem servers, a bunch of different apps, maybe even some forgotten IoT devices. Trying to get a clear picture of everything that needs checking can feel like trying to count grains of sand. You might not even know what you don’t know.
- Start with an asset inventory. Seriously, you can’t protect what you don’t know you have. This means tracking down every server, laptop, mobile device, and even software application. It’s tedious, but necessary.
- Use discovery tools. There are tools out there that can help scan your network and cloud accounts to find active devices and services. They aren’t perfect, but they give you a much better starting point than just guessing.
- Segment your network. If you can break your network into smaller, more manageable chunks, it’s easier to keep track of what’s where and what needs scanning.
The goal here is to get a handle on your attack surface, even if it’s not 100% perfect right away.
Improving Inter-Team Coordination and Communication
Fixing vulnerabilities isn’t just a security team’s job. It involves IT operations, development teams, and sometimes even business units. If these groups aren’t talking to each other, or worse, are actively working against each other, nothing gets fixed. You end up with finger-pointing and vulnerabilities lingering way longer than they should.
- Establish clear roles and responsibilities. Who is responsible for patching servers? Who handles application updates? Make sure everyone knows their part.
- Use a shared ticketing system. When a vulnerability is found, it should go into a system that everyone can see and track. This helps assign tasks and monitor progress.
- Regular sync-up meetings. Even short, weekly check-ins can make a huge difference. It’s a chance to discuss blockers, share updates, and make sure everyone is on the same page.
Managing Dynamic and Evolving Attack Surfaces
Your IT environment isn’t static. New software is installed, cloud services change, employees come and go, and attackers are always finding new ways to break in. What was secure yesterday might be vulnerable today. This means your vulnerability management can’t be a set-it-and-forget-it kind of deal.
- Automate scans as much as possible. The more you can automate the process of finding vulnerabilities, the faster you can react to new threats.
- Integrate threat intelligence. Keep an eye on what attackers are actually doing in the wild. If a new exploit is making the rounds, you need to know about it immediately.
- Re-evaluate your priorities regularly. What was a low risk last month might be a critical threat now. You need a process to constantly reassess which vulnerabilities need fixing first based on current risks.
Wrapping It Up
So, we’ve walked through how to find those pesky security holes, figure out which ones are the most dangerous, and actually fix them. It’s not a one-and-done kind of deal, though. Keeping things secure means you’ve got to keep an eye on things, check your work, and be ready to adapt when new threats pop up. Think of it like maintaining your house – you don’t just fix the leaky faucet and call it a day, right? You keep checking, you stay aware, and you make sure everything’s running smoothly. Doing this consistently helps keep your digital doors locked and your systems running right. It’s all about staying ahead of the game and making sure your organization is a tough nut to crack.
Frequently Asked Questions
What is a vulnerability management program?
Think of a vulnerability management program like a security guard for your computer systems. It’s a plan to constantly look for weak spots, figure out which ones are the most dangerous, and then fix them before bad guys can use them to get in and cause trouble.
Why is it important to fix vulnerabilities quickly?
It’s like fixing a hole in your fence right away. If you wait too long, someone could climb over and steal your stuff. For computers, this means hackers could steal important information or mess up your systems. The faster you fix it, the safer you are.
What’s the difference between fixing (remediating) and reducing (mitigating) a vulnerability?
Fixing a vulnerability is like completely patching a hole. Reducing it is like putting a temporary board over the hole – it helps for a while, but the hole is still there. Fixing is the best option, but reducing can be a good temporary solution if fixing takes too long.
How do you decide which vulnerabilities to fix first?
We look at how much damage a vulnerability could cause and how easy it is for hackers to use it. If a weak spot could cause a lot of problems and is easy to exploit, we fix that one first. It’s like dealing with the biggest dangers before the smaller ones.
Can vulnerability fixing be done automatically?
Yes, a lot of it can! We use special computer programs that can automatically find and fix many common problems, like updating software. This makes the process much faster and less likely to have mistakes.
Is fixing vulnerabilities a one-time thing?
No, it’s like brushing your teeth – you have to do it regularly! New weak spots pop up all the time, and hackers are always trying new tricks. So, we have to keep checking, fixing, and improving our security all the time.