The internet can feel like a vast, open space, but there are always people trying to find ways around the rules. This article on hackers is all about shining a light on those individuals and groups. We’ll look at who they are, what they do, and the sneaky ways they go about their business. It’s not just about the technical stuff; it’s also about understanding why they do what they do and how it affects everyone. Let’s pull back the curtain on these digital shadows.
Key Takeaways
- Hackers are individuals or groups who exploit digital weaknesses for various reasons, from financial gain to political statements.
- Different types of hackers exist, including state-sponsored actors, cybercriminals, and hacktivists, each with distinct motivations and methods.
- Common hacking tactics involve exploiting software flaws, using social engineering to trick people, and employing specialized tools.
- Digital platforms, like Twitter, can unfortunately be misused by criminals, such as human traffickers, using coded language and deceptive tactics.
- Protecting ourselves requires awareness of these threats, developing strong digital security habits, and understanding how to counter these malicious activities.
Understanding The Digital Shadows: Who Are Hackers?
The Players: Who Are The Online Spies?
So, who exactly are these digital shadows we hear so much about? The term ‘hacker’ often brings to mind images of shadowy figures in hoodies, but the reality is a lot more varied. At its core, a hacker is someone with a deep understanding of computer systems and networks, someone who can find and exploit weaknesses. These aren’t just faceless entities; they are individuals and groups with diverse motivations and skill sets. Some are driven by curiosity, others by profit, and some by a desire to make a statement. It’s a complex world, and understanding the different types of players is the first step to grasping the threats they pose.
Defining The Adversaries In Our Midst
When we talk about adversaries in the digital space, we’re really talking about people who use their technical know-how to gain unauthorized access or cause disruption. This can range from someone trying to steal your personal information for financial gain to a nation-state actor trying to disrupt another country’s infrastructure. It’s not always about breaking into systems for the sake of it; often, there’s a clear objective behind the intrusion. Think of it like this:
- Cybercriminals: These are the folks primarily motivated by money. They might use ransomware to lock up your files and demand payment, or they might steal your credit card details to make fraudulent purchases.
- Hacktivists: These individuals or groups use hacking to push a political or social agenda. They might deface a website to protest a company’s policies or leak documents to expose wrongdoing.
- State-Sponsored Actors: These are often the most sophisticated. They’re backed by governments and their goals can include espionage, intelligence gathering, or even cyber warfare.
Motivations Behind Malicious Digital Actions
Why do people hack? It’s rarely just one reason. For many, it’s about the thrill of the challenge, the intellectual puzzle of bypassing security measures. Then there’s the financial incentive, which is a huge driver for a lot of cybercrime. Imagine being able to make a living, albeit an illegal one, by exploiting vulnerabilities. For others, it’s about ideology or politics. They might see hacking as a tool to fight against perceived injustices or to advance a particular cause. Sometimes, it’s even about revenge or causing chaos for its own sake. Understanding these different motivations helps us anticipate their actions and build better defenses. It’s a constant cat-and-mouse game, and knowing your opponent’s ‘why’ is half the battle. If you’re interested in the technical side of things, exploring resources on information technology professionals can offer some insight into the skills involved.
The Diverse Landscape Of Hacker Archetypes
When we talk about hackers, it’s easy to picture a single, shadowy figure hunched over a keyboard. But the reality is way more complex. The online world has given rise to a whole spectrum of individuals and groups, each with their own reasons and methods for poking around where they shouldn’t be. It’s not just one kind of threat; it’s a whole ecosystem of digital actors.
State-Sponsored Actors: Digital Espionage And National Interests
These are the big players, often backed by governments. Think of them as digital spies working for national interests. Their goal? To gather intelligence, steal secrets, or even disrupt operations in other countries. They’re usually well-funded and have access to some pretty advanced tools. Their actions can have major geopolitical consequences, making them a serious concern for national security. It’s a high-stakes game of digital chess, and their moves are often hard to track, much like modern cyberattacks.
Cybercriminals: Driven By Financial Gain
Then you have the cybercriminals. These folks are all about the money. They might be individuals or part of organized crime rings. Their playbook includes things like ransomware, phishing scams, and stealing personal data to sell on the dark web. They’re constantly looking for the easiest way to make a buck, and unfortunately, that often means targeting regular people and businesses. It’s a business for them, albeit a very illegal one.
Hacktivists: Promoting Agendas Through Digital Means
Hacktivists are a bit different. They use their hacking skills to push a political or social message. They might deface websites, leak documents, or launch denial-of-service attacks to draw attention to their cause. Their targets are usually organizations or governments they disagree with. While their motives might seem noble to some, their methods are still illegal and can cause significant disruption.
Threat Operators And Black Market Facilitators
Beyond these main groups, there are also threat operators who manage networks of compromised computers (botnets) for various illicit purposes, like sending spam or launching attacks. And let’s not forget the black market facilitators – the ones who run the online bazaars where stolen data, hacking tools, and other illegal digital goods are bought and sold. These elements form the backbone of much of the cybercrime we see today, creating a marketplace for digital malfeasance.
The Tools Of The Trade: How Hackers Operate
So, how do these digital shadows actually get their work done? It’s not magic, though sometimes it feels like it. Hackers use a whole arsenal of methods, constantly refining their approach to slip past defenses. It’s a bit like a cat-and-mouse game, but with much higher stakes.
Common Methods Used By Online Spies
These folks are always looking for an opening. Some of the most common ways they get in involve exploiting weaknesses in software or tricking people. Think of it as finding a loose window or convincing someone to hand over the keys.
- Malware Deployment: This is a big one. Hackers create and spread malicious software like viruses, worms, and ransomware. These can steal data, lock up your files, or give the hacker control of your device.
- Phishing and Social Engineering: This is all about messing with your head. Phishing emails or messages try to trick you into clicking a bad link or giving up personal info. Social engineering takes it a step further, using psychological tricks to manipulate people into doing what the hacker wants.
- Exploiting Zero-Day Vulnerabilities: These are flaws in software that the developers don’t even know about yet. Hackers who find them can exploit them before a fix is available, giving them a significant advantage.
- Brute-Force Attacks: This involves trying countless password combinations until one works. It’s slow and noisy, but can be effective against weak passwords.
Exploiting Vulnerabilities For Unauthorized Access
Finding a vulnerability is like finding a crack in a wall. Once found, hackers can try to widen that crack to get inside. This often involves understanding how systems are built and where their weak points lie. They might look for outdated software, misconfigured servers, or weak network security. Sometimes, they use automated tools to scan for these weaknesses across many systems. The goal is always to gain access without being detected.
Social Engineering And Psychological Manipulation
This is where the human element comes into play, and honestly, it’s often the easiest way in. Hackers understand that people can be the weakest link in security. They might pretend to be someone you trust, like a colleague, a tech support person, or even a friend. They create a sense of urgency or fear to make you act without thinking. For example, an email might claim your account has been compromised and you need to click a link immediately to secure it. That link, of course, leads to a fake login page designed to steal your credentials. It’s all about playing on our natural tendencies to trust, to help, or to react quickly to perceived threats.
Human Traffickers Exploiting Digital Platforms

It’s pretty disturbing how quickly bad actors can adapt to new technologies. We’re seeing human traffickers, sadly, using the same digital tools we use every day to connect and share. It’s not just one platform either; they’re jumping between different social media sites, using each one’s unique features to their advantage. It’s like they’re playing a game, and unfortunately, real people are the ones losing.
Twitter: An Unintended Facilitator Of Modern Slavery
Twitter, with its fast-paced nature and wide reach, has become a concerning spot for traffickers. They use it to find people, make deals, and even advertise victims. It’s a place where coded messages can fly by unnoticed by most users, making it hard to spot what’s really going on. The platform’s ability to connect people instantly, while great for sharing news, also means it can connect criminals with vulnerable individuals just as quickly. It’s a stark reminder that even platforms designed for open communication can be twisted for dark purposes.
Coded Language And Deceptive Tactics
Traffickers aren’t usually posting "kidnapping for sale" ads. Instead, they get creative, using slang, emojis, and vague phrases that only those in the know understand. They might post job offers that sound too good to be true, or create fake profiles to gain trust. Sometimes they’ll use images with hidden meanings. It’s all about manipulation, playing on people’s hopes or fears to get them into dangerous situations. They might pretend to be a friend, a potential employer, or even someone offering help, only to trap their victims.
The Impact Of Digital Exploitation On Victims
Being exploited online is just as devastating as being exploited in person, and often, the two go hand-in-hand. Victims can be groomed and coerced through messages, leading to physical danger. The digital trail can be used to track and control them, making escape incredibly difficult. The psychological toll is immense, leaving lasting scars. It’s a constant battle for victims to regain control of their lives and escape the digital and physical chains that bind them.
Combating The Digital Threat: Protection And Prevention
Staying Safe In The Digital World
Look, the internet can feel like a wild west sometimes, right? With all these digital shadows lurking, it’s easy to feel a bit overwhelmed. But here’s the thing: you’re not powerless. There are practical steps we can all take to make ourselves less of a target. It’s about being smart and a little bit cautious.
First off, passwords. Seriously, ditch the "password123" or your dog’s name. Strong, unique passwords are your first line of defense. Think long, random combinations. A password manager can be a lifesaver here, helping you create and remember them all. And if a site offers two-factor authentication (2FA), use it. That extra step, like a code sent to your phone, makes a huge difference.
Then there’s what you click on. Those emails from "Nigerian princes" or urgent "bank alerts"? Be suspicious. If an email looks off, or a link seems weird, don’t click it. Hover over links to see where they actually go before committing. Your gut feeling is usually right on this stuff.
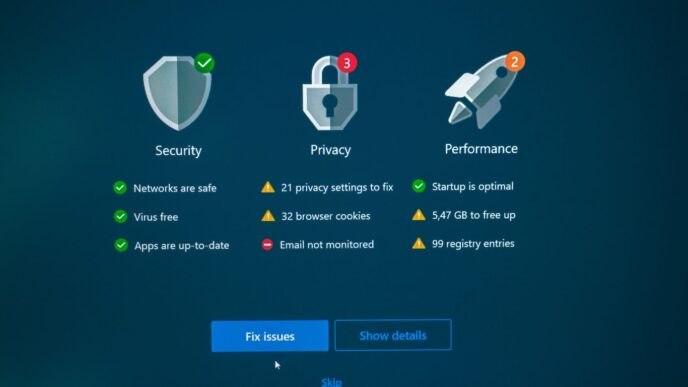
Keeping your software updated is also a big one. Those updates aren’t just annoying pop-ups; they often fix security holes that hackers love to exploit. So, update your operating system, your browser, everything. And get some good antivirus software and run scans regularly. It’s like having a digital security guard for your computer.
When you’re out and about using public Wi-Fi, a VPN is your friend. It scrambles your internet traffic, making it much harder for anyone snooping to see what you’re doing. Also, think about what you share online. Oversharing personal details on social media can give attackers a lot of ammunition. Be mindful of your digital footprint.
Developing Effective Countermeasures
Fighting back against these digital threats isn’t just about individual actions; it’s a community effort. We need to develop smarter ways to detect and stop these bad actors. This means looking at how they operate, their patterns, and their tools. By understanding their methods, we can build better defenses.
- Information Sharing: Law enforcement, cybersecurity firms, and even regular users need to share information about threats and vulnerabilities. The more we know, the faster we can react.
- Technological Innovation: We need ongoing development of security software, AI for threat detection, and encryption methods that stay ahead of the curve.
- Policy and Legislation: Governments and international bodies need to create and enforce laws that hold cybercriminals accountable and provide frameworks for cooperation.
Reclaiming Technologies From Exploitation
It’s a sad reality that technologies meant to connect us can be twisted for harmful purposes, like human trafficking. We see coded language and deceptive tactics used on platforms we use every day. The impact on victims is devastating, leaving deep emotional and psychological scars.
Our goal is to turn these tools back into forces for good. This involves educating the public about the risks and how to spot suspicious activity. Social media platforms themselves have a role to play in moderating content and identifying exploitative behavior. It’s about creating a digital environment where everyone feels safer and where exploitation is actively fought against. We all have a part in this, from reporting suspicious posts to supporting organizations working to combat these issues. It’s a collective responsibility to ensure our digital spaces are not breeding grounds for crime.
Wrapping It Up
So, we’ve looked at a lot of what goes on in the digital world, from the people behind the attacks to the ways they pull them off. It’s a bit of a mess out there, honestly. These hackers, whether they’re after money, power, or just causing trouble, are always finding new tricks. It’s not just about knowing what they do, though. It’s about remembering that real people are affected by all this. The digital tools that are supposed to connect us can unfortunately be used for some pretty bad stuff. The main thing is to stay aware. Knowing how these tactics work is the first step to protecting yourself and others. We can’t stop everyone, but we can definitely make it harder for them and try to get these technologies back to being used for good.
Frequently Asked Questions
What exactly is a hacker?
Think of a hacker as someone who’s really good at finding secret ways into computer systems, networks, or websites. They’re like digital detectives, but instead of solving mysteries, they look for weaknesses to get in without permission.
Are all hackers bad guys?
Not at all! Some hackers, called ‘white hat’ hackers, use their skills for good. They find security problems and tell the owners so they can fix them before bad guys do. Others, like ‘black hat’ hackers, use their skills to do illegal things for money or other bad reasons.
Why do hackers do what they do?
Hackers have different reasons. Some want money, like thieves. Others might want to cause trouble for a cause they believe in, like activists. Some are even hired by governments to spy on other countries. And sadly, some use their skills to hurt people, like human traffickers.
What are some common ways hackers try to get in?
Hackers use lots of tricks! They might send fake emails that look real to trick you into giving them passwords (that’s called phishing). They also look for software that has bugs or mistakes that they can use to break in, or they might try to trick people into giving them information through conversations.
How can I protect myself from hackers?
It’s important to be careful online. Use strong, unique passwords for different accounts and don’t share them. Be suspicious of emails or messages asking for personal information. Keep your computer and phone software updated, as updates often fix security problems.
How do human traffickers use the internet?
Sadly, traffickers use online platforms like Twitter to find and trick people, especially young ones. They might use secret codes or fake profiles to hide what they’re doing. They exploit technology to find victims and control them, which is a terrible form of modern slavery.